Contents
- Introduction
- What is Computer Forensic?
- Roles, Objectives and Priorities
- Types of digital evidence
- Digital forensics tools and techniques
- Steps in a digital forensic investigation
- Skills needed for Cyber Forensics
- Ethical issues in digital forensics
- Digital forensic certification and training
- Job Prospects
- Conclusion
Introduction
 In today's world, where technology has infiltrated every aspect of our lives, digital evidence has become an integral part of almost all criminal investigations. This is where computer forensics, the scientific examination of digital devices, comes into play. From recovering deleted files to investigating complex cyber-attacks, the scope of computer forensics is vast and ever-expanding.
In today's world, where technology has infiltrated every aspect of our lives, digital evidence has become an integral part of almost all criminal investigations. This is where computer forensics, the scientific examination of digital devices, comes into play. From recovering deleted files to investigating complex cyber-attacks, the scope of computer forensics is vast and ever-expanding.
Whether you're a law enforcement professional, a cybersecurity expert, or just someone looking to better understand the world of digital forensics, this tutorial will provide you with a comprehensive overview of the scope of Computer Forensics. I shall explore the tools and techniques used by forensic experts to uncover digital evidence, and take a closer look at how this evidence is being used to solve complex cases in today's digital age.
Fasten your seatbelts and get ready to embark on a journey into the fascinating world of computer forensics!
Let's go ahead with the first step by discussing the simple definition of Computer Forensics.
What is Computer Forensic?
 Have you ever wondered how digital detectives crack down on cybercriminals? That's where computer forensics comes in! It is the collection, preservation, analysis, and presentation of computer-related evidence. With the rise of technology in our everyday lives, the need for skilled forensic investigators has never been greater.
Have you ever wondered how digital detectives crack down on cybercriminals? That's where computer forensics comes in! It is the collection, preservation, analysis, and presentation of computer-related evidence. With the rise of technology in our everyday lives, the need for skilled forensic investigators has never been greater.
In a nutshell, Computer Forensics is the investigation of a computer or other device to gather and present digital evidence in a court of law. It is also called Digital Forensics or Cyber Forensics.
The goal of Computer Forensics is to perform an investigation and document a chain of evidence to find out what happened on the device and who was responsible.
"It can be used as part of data recovery to gather data from a crashed server, failed drive, reformatted operating system, or other situation where a system has unexpectedly stopped working."
Roles, Objectives and Priorities
Why do we feel the demand for Computer Forensics?
Digital forensics is used to investigate and analyze digital devices, networks, and digital media to gather evidence for legal or investigative purposes.
- Criminal investigations: Digital forensics can be used in criminal investigations to collect evidence that can be used in court. This can include evidence of hacking, cybercrime, and other digital criminal activities.
 Corporate investigations: Digital forensics can also be used in corporate investigations to identify employee misconduct, intellectual property theft, and other types of fraud.
Corporate investigations: Digital forensics can also be used in corporate investigations to identify employee misconduct, intellectual property theft, and other types of fraud.- Incident response: Digital forensics can be used to investigate security incidents such as network breaches, data breaches, and cyber-attacks.
- Civil litigation: Digital forensics can be used in civil litigation to support legal claims or defenses. For example, digital forensics can be used to investigate allegations of harassment, discrimination, or wrongful termination.
- Regulatory compliance: Digital forensics can be used to ensure compliance with laws and regulations related to data retention, data privacy, and information security.
Types of digital evidence
 In digital forensics, there are several types of digital evidence can be collected and analyzed. The specific types of evidence that are relevant to a case will depend on the nature of the investigation. and the type of device or media being inspected.
In digital forensics, there are several types of digital evidence can be collected and analyzed. The specific types of evidence that are relevant to a case will depend on the nature of the investigation. and the type of device or media being inspected.
- Computer files: This includes any type of digital files, such as documents, spreadsheets, images, videos, and audio files.
- Email messages: Emails can be a rich source of digital evidence, as they often contain important information about a person's activities, contacts, and communications.
- Internet activity: This includes web browsing history, search engine queries, and social media activity.
- Network traffic: This includes data packets that are transmitted over a network, which can provide information about the types of communication occurring between different devices.
- Mobile devices: Mobile devices, such as smartphones and tablets, can contain a wide range of digital evidence, including call logs, text messages, emails, and app usage data.
- Cloud data: Cloud storage and applications can also be a rich source of digital evidence, as they often contain important data that can be used to investigate a case.
Digital forensics tools and techniques
The Cyber Forensic field is constantly evolving, and new tools and techniques are regularly being developed to help investigators stay ahead of the latest threats and challenges.
- EnCase: A powerful digital forensics tool used for analyzing and preserving digital evidence.
- Forensic Toolkit (FTK): Another popular digital forensics tool used for collecting, analyzing, and preserving digital evidence.
 Volatility: A free, open-source tool used for memory forensics, which involves analyzing data stored in a computer's RAM.
Volatility: A free, open-source tool used for memory forensics, which involves analyzing data stored in a computer's RAM.- Wireshark: A network protocol analyzer used for analyzing and troubleshooting network issues, as well as for network forensics.
- Autopsy: An open-source digital forensics tool that is user-friendly and can be used for analyzing a wide range of digital media.
- Sleuth Kit: A set of open-source tools used for digital forensics and incident response.
- Live forensics: A technique used for analyzing a running system without shutting it down, which can help preserve volatile data.
- Timeline analysis: A technique used for analyzing digital evidence over time, which can help identify patterns and sequences of events.
- Data carving: A technique used for recovering deleted or damaged files from digital media.
- Steganography detection: A technique used for detecting hidden messages or files within digital media, which can be used for cybercrime investigations.
Steps in a digital forensic investigation
Digital forensic investigations can be complex! The specific steps and techniques used will depend on the nature of the investigation and the types of evidence involved. It is important to follow established procedures and best practices to ensure the integrity of the evidence and the effectiveness of the investigation.
 Identify the scope and goals of the investigation: The first step is to identify the nature of the case, the devices or media to be analyzed, and the goals of the investigation. This will help determine the scope of the investigation and the types of evidence that need to be collected.
Identify the scope and goals of the investigation: The first step is to identify the nature of the case, the devices or media to be analyzed, and the goals of the investigation. This will help determine the scope of the investigation and the types of evidence that need to be collected.- Secure the digital evidence: Once the scope has been identified, the next step is to secure the digital evidence to prevent tampering or loss of data. This may involve creating forensic copies of the original data or locking down devices to prevent data from being altered or destroyed.
- Conduct a preliminary analysis: After securing the evidence, the investigator will conduct a preliminary analysis to identify the types of data that are present and to determine what tools and techniques will be needed to analyze the data further.
- Analyze the digital evidence: The next step is to analyze the digital evidence using a variety of tools and techniques, such as file carving, keyword searching, and timeline analysis. This may involve analyzing data from multiple sources, such as hard drives, mobile devices, and cloud storage.
- Document the findings: Throughout the investigation, it is important to document all findings and processes to ensure the integrity of the evidence and to create a clear record of the investigation.
- Present the findings: Finally, the investigator will present the findings to the appropriate stakeholders, such as law enforcement, attorneys, or corporate management. This may involve creating reports, testifying in court, or providing guidance on the next steps.
Skills needed for Cyber Forensics
- Log Analysis
- Endpoint Data Collection
- Dark Web Monitoring
- Malware Analysis
- Tools and Techniques
Ethical issues in digital forensics
Digital forensics can raise several ethical issues, including:
- Privacy: Digital forensics can involve analyzing personal data and communications, which can raise privacy concerns. Investigators must ensure that they are only collecting and analyzing data that is relevant to the case and that they are complying with applicable laws and regulations.
- Bias and fairness: Investigators must strive to be objective and unbiased in their analysis and reporting of digital evidence. They must also ensure that their methods and techniques are reliable and accurate and that they are not relying on faulty assumptions or stereotypes.
 Informed consent: In some cases, investigators may need to obtain the consent of individuals before analyzing their digital devices or data. This may be particularly important in cases involving employee-owned devices or personal accounts.
Informed consent: In some cases, investigators may need to obtain the consent of individuals before analyzing their digital devices or data. This may be particularly important in cases involving employee-owned devices or personal accounts.- Data retention: Investigators must ensure that they are properly preserving digital evidence and that they are not altering or destroying data in the course of their investigation. They must also ensure that they are complying with any relevant data retention policies or regulations.
- Confidentiality: Investigators must ensure that they are protecting the confidentiality of digital evidence and that they are not sharing or disclosing data inappropriately. They must also ensure that they are complying with any applicable legal or ethical standards for the handling of confidential information.
- Transparency and accountability: Investigators must be transparent about their methods and techniques and be able to explain their findings to relevant stakeholders. They must also be accountable for their actions and decisions, and be willing to answer questions and address concerns from others involved in the investigation.
Digital forensic certification and training
Looking to start a career in digital forensics? Look no further! This highly promising career is offering a wide range of education to help you develop the skills you need to succeed in this exciting field.
 From beginner courses that cover the basics of Computer Forensics to advanced programs that delve into the latest techniques and tools, there is something for everyone. Whether you're interested in working for law enforcement, private investigation, or cybersecurity.
From beginner courses that cover the basics of Computer Forensics to advanced programs that delve into the latest techniques and tools, there is something for everyone. Whether you're interested in working for law enforcement, private investigation, or cybersecurity.
Maybe you are thinking about which courses you must do to reach your goal! Here you go.
Digital forensic certification and training provide individuals with the necessary skills and knowledge to investigate and analyze digital devices for legal and investigative purposes. This field requires professionals to be well-versed in computer systems, networks, and digital media to extract and interpret digital evidence.
This program typically covers topics such as data acquisition, evidence preservation, analysis techniques, and report writing. Certification programs are offered by various organizations, including the International Association of Computer Investigative Specialists (IACIS), the International Society of Forensic Computer Examiners (ISFCE), and the SANS Institute. These programs help professionals stay current with the latest techniques and technologies in the field and enhance their credibility in the eyes of potential employers.
Be careful about a program with benefits!
Job Prospects
Digital forensics is a growing and promising field, and there are many job opportunities available for individuals who have the necessary skills and knowledge. Here are some of the job prospects in digital forensics:
- Digital Forensic Analyst: A digital forensic analyst is responsible for conducting forensic investigations and analysis of digital evidence. This may include analyzing computer systems, mobile devices, and other electronic devices to uncover evidence of cybercrime, fraud, or other illegal activities.
 Incident Response Analyst: An incident response analyst is responsible for investigating and responding to security incidents, such as network breaches or cyberattacks. They work closely with digital forensic analysts to analyze and contain security incidents and to identify and prevent future attacks.
Incident Response Analyst: An incident response analyst is responsible for investigating and responding to security incidents, such as network breaches or cyberattacks. They work closely with digital forensic analysts to analyze and contain security incidents and to identify and prevent future attacks.- Forensic Computer Examiner: A forensic computer examiner is responsible for examining digital evidence in criminal investigations. They may work for law enforcement agencies or private investigative firms and may be involved in cases such as cyberstalking, hacking, or identity theft.
- Cybersecurity Analyst: A cybersecurity analyst is responsible for monitoring and analyzing networks and systems for security threats. They may use digital forensic tools to identify and investigate security incidents and may work to develop and implement security solutions to prevent future attacks.
- Digital Forensic Consultant: A digital forensic consultant is responsible for providing expert advice and guidance to organizations on digital forensic matters. They may work with legal teams or law enforcement agencies to provide expert testimony in court cases, or they may work with private companies to develop and implement digital forensic strategies.
Can you imagine how much a Digital Forensic Analyst earns per year? The salary of a digital forensic analyst varies depending on several factors such as the level of experience, education, location, and industry.
A general overview of the average salaries of digital forensic analysts in India and outside India. Look at a glance!
Inside India:
- Entry-level digital forensic analyst: INR 3-5 lakhs per year (approximately).
- Mid-level digital forensic analyst: INR 6-10 lakhs per year (approximately).
- Senior-level digital forensic analyst: INR 10-20 lakhs per year (approximately).
Outside India:
- Entry-level digital forensic analyst: USD 50,000-70,000 per year.
- Mid-level digital forensic analyst: USD 80,000-120,000 per year.
- Senior-level digital forensic analyst: USD 120,000-150,000 per year.
Conclusion
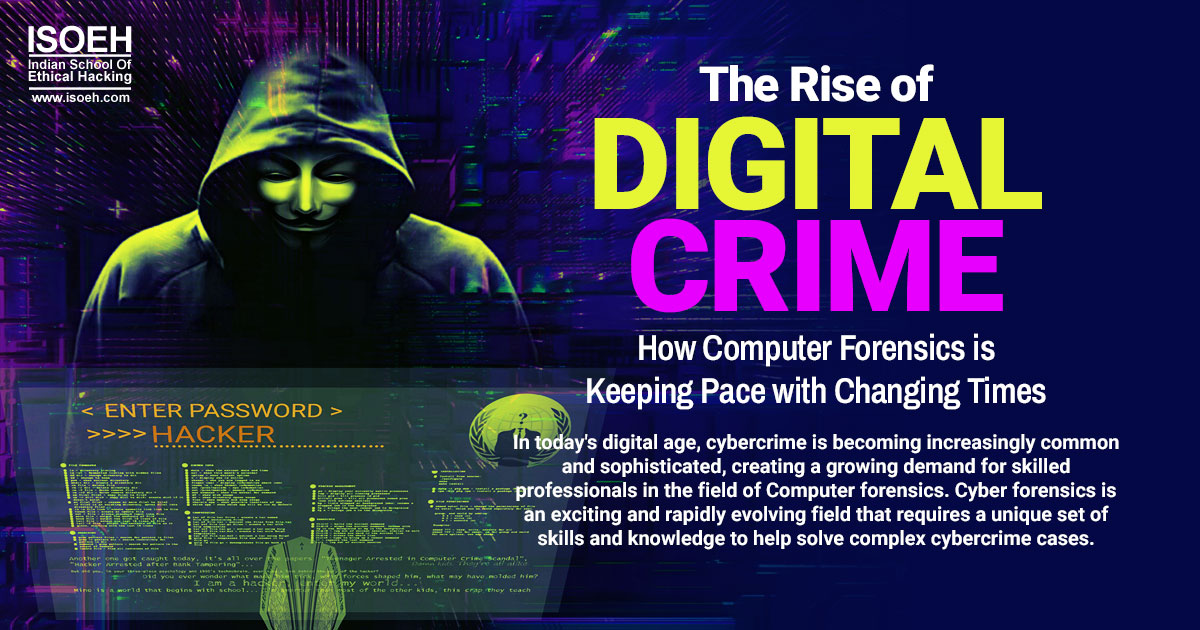
In today's digital age, cybercrime is becoming increasingly common and sophisticated, creating a growing demand for skilled professionals in the field of Computer forensics. Cyber forensics is an exciting and rapidly evolving field that requires a unique set of skills and knowledge to help solve complex cybercrime cases.
By pursuing a high-promising career in digital forensics, you can play a vital role in combating cybercrime and protecting individuals, organizations, and society as a whole. Whether you're a seasoned IT professional or just starting your career, digital forensics offers a wealth of opportunities for growth and advancement.
So why not enroll in a Computer forensics course today and join the ranks of digital forensic experts who are shaping the future of cybersecurity? With the right training and skills, you can make a real difference in the fight against cybercrime and help create a safer, more secure digital world for us all.
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details