In the software world reverse engineering boils down to taking an existing program for which source-code or proper documentation is not available and attempting to recover details regarding its’ design and implementation.
Software reverse engineering is a purely virtual process, involving only a CPU, and the human mind which integrates several arts: code breaking, puzzle solving, programming, and logical analysis.
It's major application is in the area of malware analysis, computer forensics, giving protection to software so that it becomes hard to get the source code of it.
Duration
40 hours - 2 classes per week
Eligibility
- Knowledge of C programming
- Knowledge of Assembly programming language(desirable)
Course Fees
Class Room Training
Rs.40,000/-
Inclusive of all taxes
Online Training
Rs.50,000/-Rs.40,000/-
Inclusive of all taxes
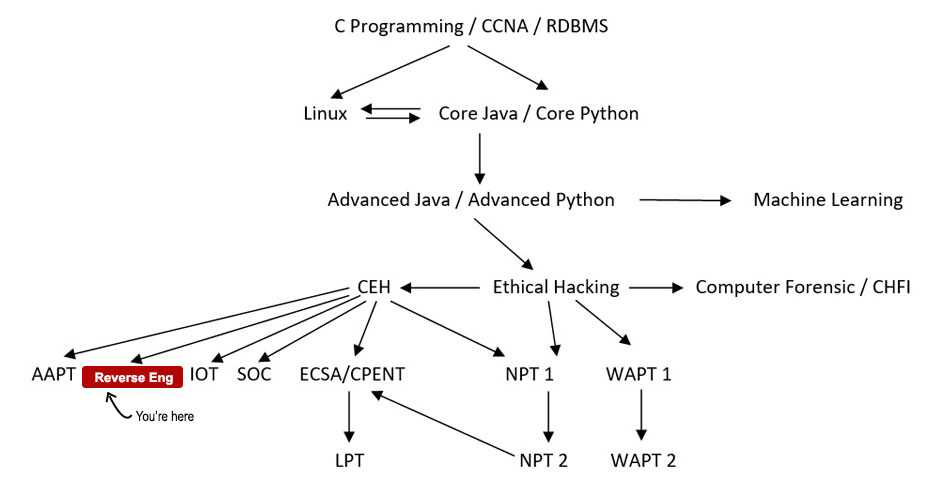
Your Course Path
Course Details
Module 01: Introduction to Reverse Engineering
- What Is Reverse Engineering?
- Why Reversing an application is required?
- Basic Perquisite for learning Reverse Engineering
- The responsibility of Reverse Engineer
Module 02: Windows Architecture
- User and Kernel mode fundamentals
- Memory management
- Process and Threads
- File Systems
- Windows I/O
Module 03: Assembly Language Fundamentals
- What is Assembly Language?
- Difference between Assembly Language and other high level language
- Fundamentals of different registers
- Instructions of Assembly Language
- "Hello World" in Assembly Language
- Assembly Language in Reverse Engineering
Module 04: Windows PE Format Analysis
- Basic structure of PE
- The DOS Header
- The PE Header
- The Section Table
- Virtual address (VA) and Relative Virtual Address (RVA)
- Offset
Module 05: Application Cracking
- Definition of Application Cracking
- Different kind of Patching
- Serial Fishing
- License Key
- Manual Unpacking
- Key-genning
- Obfuscation
- Unpacking Packed/Protected Executables
Module 06: Tools for Reverse Engineering
- Introduction to Ollydbg
- Various Plugins in Ollydbg
- "Hello World" Application Reversing with Ollydbg
- Application Key-genning with Ollydbg
- Anti Debugging Technique Bypass with Ollydbg
- Live Demonstration with various tools
Module 07: Reversing Technique of VB Application
- Basic of Visual Basic
- Tools for Reverse VB Application
- Detailed Analysis of VB Application
Module 08: Reversing Technique of DotNet Application
- Basic of DotNet Frame Work
- Tools for Reverse DotNet Application
- Detailed Analysis of DotNet Application
Module 09: World of Malwares
- What is Malware?
- Kinds of Malware
- Why Malware is being created?
- Various Terminology about Malware
Module 10: Malware Analysis Lab Setup
- Creating your own Virtual World
- A Copy of Windows XP / 7
- Tools for analysis of the Windows Malware
- Prohibition on Connection Between Virtual System and Host System
Module 11: Basic Static Analysis of Malware
- Anti-Virus Scanning
- Hashing: Fingerprint of Malware
- Detecting Packers
- Analysing PE file Headers and Sections
Module 12: Basic Dynamic Analysis of Malware
- Running Malware using Sandboxie
- Analysing the Process of Malware
- Monitoring Registry Changes
- Network Traffic Analysis
Module 13: Advanced Malware Analysis
- Patterns of common Malware Characteristics at the Windows API level
- Unpacking Malware
- Recovering concealed malicious code and data
- Bypassing anti-analysis defences
Enroll Now
Fields marked with * are mandatory.


