Social Engineering is nothing but psychological manipulation to trick users into making security mistakes or giving away sensitive and confidential information. The idea behind social engineering is to understand and predict the potential victim's psyche and natural tendencies and emotional reactions and squeeze information without any code. It is a non-technical strategy for cyber attackers and doesn't necessarily involve the compromise or exploitation of software or systems.
As social engineering attacks continue to grow in sophistication and frequency, companies should look into creating awareness among the employees and educating them about security do's and don'ts. As employees are the last lines of defense for any company. That firewall won't be of much use if users are tricked into clicking on a malicious link they received via email or from a Facebook friend or Linkedin connection.
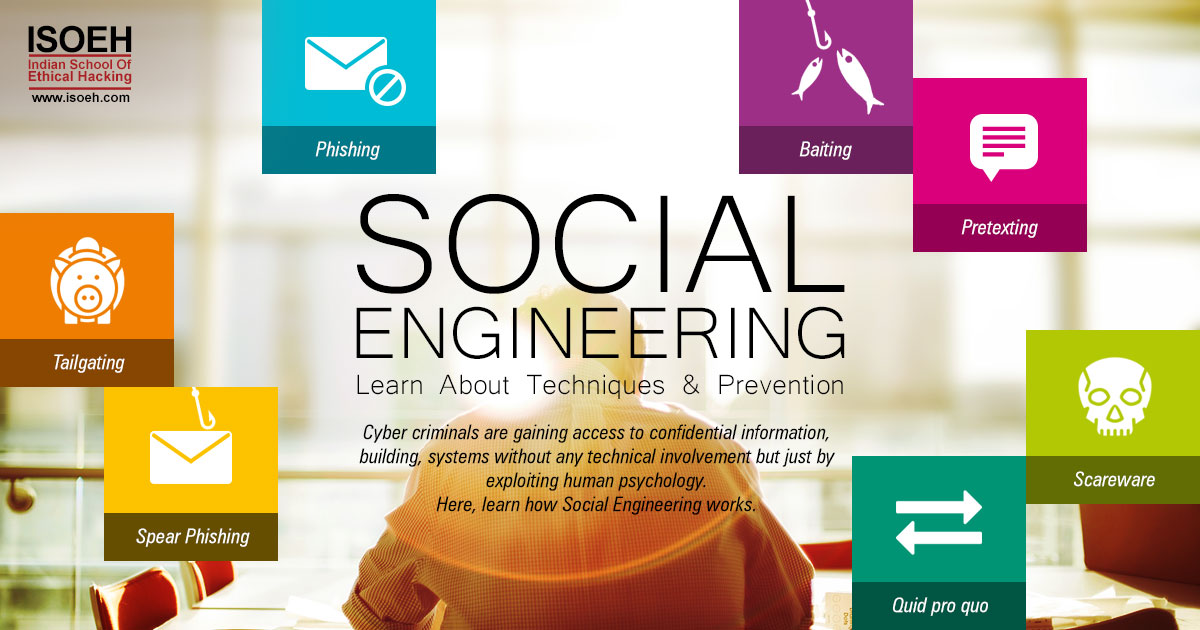
Types of Social Engineering attacks:
The attacks come in many different forms and can be performed where human interaction is involved. Educating employees on the common types of social engineering attacks like – baiting, phishing, pretexting, tailgating etc. can reduce half the risk. Their understanding of these common social engineering tactics is ultimately the best defense to prevent any breach. There are technological solutions too that help to mitigate social engineering tactics such as – email filters, firewalls and network and data monitoring tools.
However, let's have a look at the common social engineering attacks:
1. Phishing:
The attacker makes fraudulent communication with the victim that is disguised as legitimate, often claiming or seeming to be from a trusted source. The perpetrator typically sends an email or text to the target, seeking information that might help with a more significant crime. The recipient is manipulated into installing malware on their device or sharing personal, financial or business information. Though email is the most popular mode of communication for phishing attacks but now phishing also utilizing chat applications, social media, phone calls, spoofed websites designed to look legitimate.
2. Baiting:
As its name implies, baiting attacks use a false promise to pique a victim's greed or curiosity. They lure users into a trap that steals their personal information or inflicts their systems with malware. Attackers leave a malware infected device – such as a USB flash drive or CD in a place where someone likely will find it. Victims pick up the bait out of curiosity and insert it into a work or home computer which results in automatic malware installation on the system. Online forms of baiting consist of enticing ads that lead to malicious sites or that encourage users to download a malware-infected application.
3. Pretexting:
Pretexting occurs when an attacker obtains information through a series of cleverly crafted lies. The aim is to lure the victim into providing access to sensitive data or protected systems. The scam is often initiated by a perpetrator pretending to need sensitive information from a victim so as to perform a critical task. All sorts of pertinent information and records are gathered using this scam, such as social security numbers, personal addresses and phone numbers, phone records, staff vacation dates, bank records and even security information.
4. Scareware
The motif of Scareware is to terrify the victim with false alarms and fictitious threats. You might have encountered with popup banners appearing on your browser while surfing web displaying such text as, “Your computer may be infected with harmful spyware programs.” Naturally, you tend to click on the malicious link which either prompts to install a malware-infected tool or directs you to a malicious site where your computer becomes infected. Scareware is also distributed via spam email containing bogus warnings and offers.
5. Quid pro quo
This strategy involves an exchange. Attackers request private information from the victim in exchange for something desirable or some type of compensation. For example, if someone asks you for a login credential in exchange for an exciting gift, then remember this is just too good to be true.
6. Tailgating
Tailgating, also known as piggy banking, is a physical social engineering technique that is affecting business largely. Tailgating is often described as the passage of unauthorized personnel, either forced or accidental, behind that of an authorized user. Tailgating could occur when someone asks you to hold the door open because they forgot their access card or asks to borrow your phone or laptop to complete a simple task and instead installs malware or steals data. For service industries such as the leisure industry, where controlled access is required, this can result in a loss of revenue.
7. Spear Phishing
Spear phishing is a more targeted version of a phishing scam that focusses on a particular individual or organization. Attackers customize their messages based on characteristics, job positions, and contacts belonging to their victims to make their attack less conspicuous.
Often times this information is taken from victims' social media accounts or other online activity. By personalizing their phishing tactics, spear phishers have higher success rates for tricking victims into granting access or divulging sensitive information such as financial data or trade secrets.
How to avoid being a social media victim?
Social Engineering is totally based on exploiting human emotions and reactions. The idea is to draw your attention and make you fall into their trap. So, being alert is the only way out to protect yourself against most social engineering attacks taking place in the digital realm. Here, few tips for your safety:
- Don't open emails from the suspicious sources – even if you know the person, crosscheck and confirm. You never know if the email id is spoofed or not! Even an email purportedly coming from a trusted source may have actually been initiated by an attacker. No matter how legitimate that email appears, it's safer to type a URL into your browser instead of clicking on a link.
- Think twice before accepting a tempting offer. Google it before making any step to confirm whether it's a trap or not.
- User credentials are the valuable information that attackers are seeking for. Using multifactor authentication can help you ensure your account's protection if there is any system compromise.
- Social engineers want you to panic and react quickly without giving much thought. If you find something suspicious, stop and slow down and consider that a scammer might be behind the email or phone call. Instead of panicking and taking action, stop, think and act in your best interest.
- Make sure your computer and other devices are running an updated version of antivirus software. If possible, set the operating systems to update automatically. This will ensure your system to prepare for the latest security threats.
- There is email software available to filter out junk email, including scams. Set your spam filters high so that it weeds out as much junk emails as possible.
Cyber attackers are after information and highly sophisticated social engineering methods are a big concern for organizations and individuals. Education is the first step to prevent yourself and your organization from falling victim to these skilled attackers. Remember, social engineering strategies may apply to both online and offline. The best way to deal with it is, stay vigil.
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details