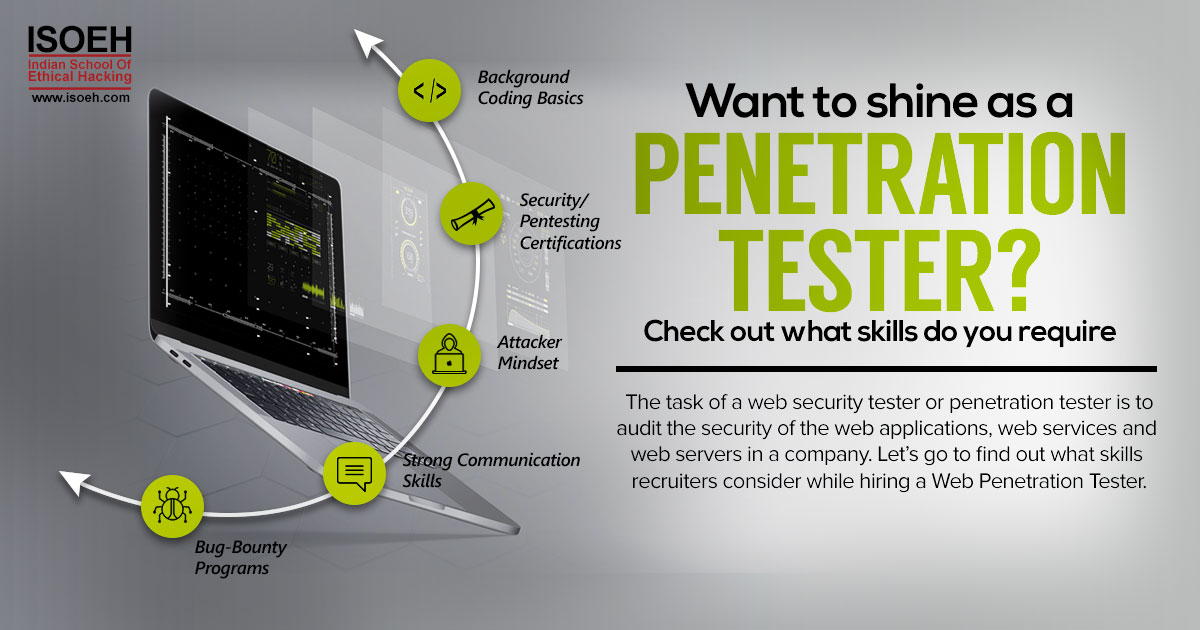
If you are inquisitive by nature and dream to become a successful bug bounty hunter, the first thing you need is consistent, if not constant, attention. As IT security is becoming the talk of the town, more and more companies are focusing on conducting Bug Bounty programs to make their software more secure. Hackers with sufficient skills are paid to find vulnerabilities in websites and software. Bug bounty programs allow skilled hackers to hack into their systems as long as any security holes are reported to company before disclosing them publicly.
So, what kind of vulnerability you should be looking for?
As a bug hunter, the best way to practice is, building things by writing codes and then going back to crack it. The bug bounties find the loopholes in any website or software, which may allow accomplishing something that one should not be able to. Some of the usual vulnerabilities are:
- XSS – Cross Site Scripting. Injecting JavaScript code into a web page that another user is visiting.
- SQLi – SQL Injection. Injecting SQL commands into a SQL query that is run against a production database.
- RCE – Remote Code Execution. Running your code or commands on someone else's server.
- IDOR – Insecure Direct Object References. When you access secret data by manipulating an ID.
- CSRF – Cross Site Request Forgery. Executing actions on another user’s behalf by secretly submitting a form to another site.
How to do it?
There are 3 major steps to get started. Scoping and recon, bug identification and exploitation.
- If you want to identify more bugs in less time then it’s important to scope your target organization. Carefully read the terms of the program in order to avoid submitting things that aren’t within the scope of the bounty program. The larger the potential attack surface, higher the chances of finding possible vulnerabilities.
- After finding out the scopes, it's time to find the sub domains. Pick up interesting URLs through Burp Suite’s spider tool and proceed towards the next step i.e content discovery. Take your time while performing Recon until you are completely clear about how the site operates. If there’s an unusual domain, clear your spider’s queue and spider that domain specifically. Finding a bug on the program’s flagship application is undoubtedly the best thing, but competition will be high there. So, try to look for those forgotten sub domains that are not updated or running a vulnerable version of Apache.
- The next step is, bug identification. At this step, you can try out Cross site scripting. They run in browsers without affecting other users. Burp suite extensions like Reflector may help you while hunting for cross-site scripting. It shows you which parameters are reflected back into the response. But never forget about platform specific vulnerabilities.
- The final step is exploitation. Once the existence of the bug is proven, it’s time to unleash the level of severity associated with it. It’s important to describe some scenarios of exploitation. The more severe vulnerability receives the higher reward. So, it’s best to accomplish some tests to see how far you can take the vulnerability before submitting the report. And always remember, if you notice a vulnerability being blocked by a WAF, don’t assume it can’t be exploited. Instead, try to bypass the WAF and get a working PoC to exploit the vulnerability and no one can stop you from being paid.
In case of more serious vulnerabilities, some programs will state what to do to prove the vulnerability. One should not ever go beyond this.
After you are done with all the steps, here are few tips to make the report:
- Make sure to prepare a report in a clear and concise manner. Explain the risk in details, instead of providing the links to the vulnerabilities.
- Present it with step by step instruction to reproduce the vulnerability which will be easy to follow.
- Use your professional email id if you are making a PoC to explain your report. Keep your PoC short and crisp.
- Submit a report that’s neither too short nor long without any grammatical or spelling error.
- Do not disclose the vulnerability to anyone or post it on social media until you receive the outcome of your report.
Bug reporting is all about patience. It may take lots of blood and sweat on submission of a vulnerability only to find out that it had been previously reported. Or otherwise, you may receive some easy cash payouts as the reward of your hard work. But, one thing you’ll gain for sure is knowledge. Just dive into finding possible vulnerabilities and learn along the way. Happy hunting!
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details