In the last few decades, we have developed the habit of relying too much on our mobile devices. All our personal details along with social communication history are now within our devices which can be available to anyone who gets hold of the device, easily. All our banking details, browsing history, chat sessions, whereabouts, personal photos etc. are stored in phones which can be manipulated anytime if it gets hacked. Government spying is an open secret now and both government and private organizations are into cyber spying techniques to squeeze information and intelligence as much as possible. So, it's important to consider your mobile security seriously to protect your data from intruders.
Here, revealing 5 ways your phone can get hacked and how you can prevent it.
Snooping via public Wi-Fi
We have a tendency to connect our devices to unknown public Wi-Fi without considering the security aspects where open Wi-Fi is one of the most popular ways to compromise any device. It is easy to view all the unencrypted traffic from unsecured Wi-Fi network. You could be presented with a lookalike site which would demand to enter your details. These are designed in a pretty convincing way to capture your username and password. Hackers often opt for the name of genuine hotspot and set up a fake access point to grab data.
What you can do:
- Avoid connecting with unfamiliar Wi-Fi network with suspicious logo or typos or inaccuracy
- Never use public Wi-Fi for mobile banking or shopping
- Download a VPN app to encrypt your Smartphone traffic
- Never enter private information unless it's a secured site. Look for “https” in the URL and a green lock icon in the address bar.
- Always remember to sign out ending your session when you’ve finished else a sidejacker (session hacker) could continue your web session on site you were in through cookies and HTTP packets.
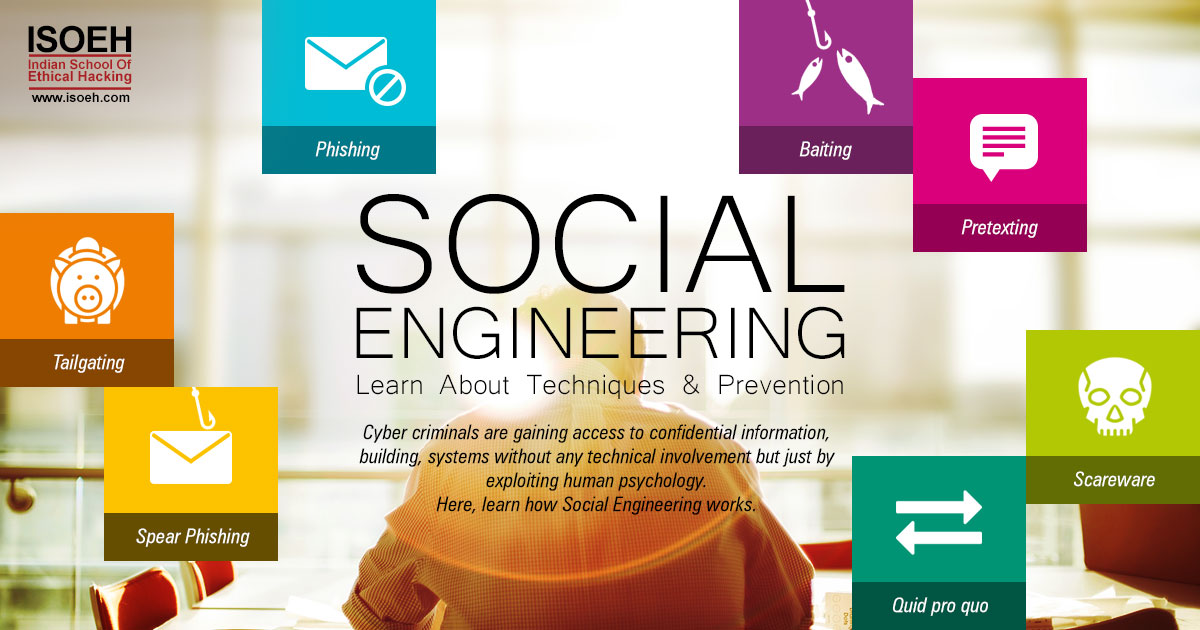
Phishing
The most successful 'hacker tool' to trick the recipient into taking the attacker's desired action such as providing login credentials or other sensitive information posing as a trustworthy entity or organization. Phishing can be accomplished through emails containing malicious attachments which are sent in such a clever way that people are likely to open it. Emails from banks or financial institutions or web service are considered important and people are most likely to click on the attachments and eventually become the victim of grave cyber attack.
This can expose user’s phone data or contain a phishing overlay designed to steal login credentials. This method is hard to detect but there are key indicators to know that your phone has been compromised. Be aware of emails with generic greetings, requesting personal information or an urgent response, or containing spoofed links.
What you can do:
- Ignore emails of embedded forms with strange attachments or suspicious web links.
- Avoid clicking links from the numbers unknown to you or vague messages from a trusted source if you can’t see the full URL.
- Keep in mind how you usually verify your identity. If a mail is prompting you to do it some other way, think twice. For example, your bank will never ask you to input your full password or PIN.
- If you end up downloading an app by clicking on the link, your phone should notify you. Delete the app immediately or run a mobile security scan.
Installing Spy Apps
There are few apps that allow remote access to a device. Such apps can be used to view text messages, emails, internet history and photos, log phone calls and track the GPS. It can also record conversations by hijacking the phone’s mic. In short, the apps would allow anything a hacker would possibly want to do with your phone. There are a lot of fake apps available in the market to cause you unwanted problems. Fake apps often include intrusive pop-ups asking for your personal details and are often difficult to delete. So, how can you spot a fake app? Here’s the checklist:
- Check the app details, review, publisher, amount of downloads, proper logo, editor's choice tick which confirms its legitimacy.
- Search for the app online to see if there any mobile variation exists.
- Be careful of fake apps offering discounts or lucrative deals. It might be a strategy to draw people's attention.
"There aren't too many indicators of a hidden spy app – you might see more internet traffic on your bill, or your battery life may be shorter than usual because the app is reporting back to a third-party," says Chester Wisniewski, principal research scientist at security firm Sophos.
What you can do:
- Go through your app list and delete the ones you don't recognize.
- Don't jailbreak your phone to avoid letting spywares hide deep inside the device. Sometimes, even security software fails to detect a spy app.
- Secure your phone with a strong password which no one can guess.
- Android users can download a mobile security app which will flag malicious programs.
Software Update
We often get pop-up updates from third-party programs which are not only annoying but also can be a potential threat to your device. In the name of software update, you might end up installing malware or spywares.
If you find the interface of the software is suspicious, then it probably is. If it asks for any additional login or personal info then it could be malicious.
What you can do:
- Check whether the software update is coming from the publisher’s original website and not a link to an alternative site.
- Pay attention to the HTML address of the site.
- Free software services should never send email alerts for an immediate update.
- Check for 'review' option in their notification
Unrecognized access to Google account
Gmail is the primary email for many users. So, hacking a Gmail account exposes a huge amount of personal data backed up from your Smartphone. This means the attacker can get hold of your photos, contacts, current location, messages, call logs etc. The effect can get worst if the account is linked with your social media accounts leading to your mobile carrier account which can broaden the path of identity theft ultimately damaging your reputation.
Online criminals know that the information is important to the owner and this can lead to accounts and their content being held digitally hostage unless the owner agrees to pay a ransom.
What you can do:
- Create a strong password for these key accounts which will be impossible to guess for anyone.
- Enable two-factor authentication to make sure that one can’t access your account without accessing your phone.
- Lie when setting up password security questions and trick the attacker; thus you can prevent an attacker to reset your password. Make sure, you remember your answer!
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details