For Enquiry, please email us info@isoeh.com
For any complaint, write directly to CEO - sandeep@isoeh.com


Courses
Home
- All Courses
- CompTIA Global Courses
-
EC-Council Global Courses
- Certified Ethical Hacker - CEH v13 - AI Powered
- CEH Master
- Certified Penetration Testing Professional - CPENT
- CHFI v11 - Computer Hacking Forensic Investigator
- Certified SOC Analyst (CSA)
- Certified Cybersecurity Technician - CCT
- Certified Cloud Security Engineer - CCSE
- Web Application Hacking and Security - WAHS
- Certified Network Defender - CND v2
- EC-Council - Cyber Security Programs
- Post Graduation Courses
- Graduation Courses
- PG Diploma Courses
- Diploma Courses
- Vocational Training Courses
-
Skill Development Short Term Courses
- Ethical Hacking
- Computer Forensic
- SOC Analyst Fundamental
- Core Python Programming
- Advanced Python Programming
- CCNA Essentials & Ethical Hacking Combo
- Web Application Penetration Testing Level I
- Web Application Penetration Testing Level II
- Network Penetration Testing Level I
- Network Penetration Testing Level II
- Reverse Engineering & Malware Analysis
- Bug Bounty Hunting
- CCNA Essential
- Firewall Administration
- A-Z Defense in Comp Security - For Corporates
Bhubaneswar: +91 8100442829
Siliguri: +91 9007392360, +91 8100442827
What goes into selecting a Web Pentesting consultant?
Require Further Information
- OWASP Top 10 Concepts
- Decent Development Background Coding Basics
- Having a Hacker thinking psychology
- Knowledgeable in UNIX/Linux
- Participated in Bug Bounty Programs(Added Bonus)
- Attended a security conference
- Has published exploits or disclosures in Exploit-DB, Packet Storm, or other Vulnerability Databases
- Security certification is also a plus
- Knowing to code helps an pentester to understand white box logic
- Familiarity with OWASP top-10 helps design POCs and the know how of application vulnerabilities and attack vector
- Bug Bounties and Disclosures proves his/her research oriented bent of mind showing him as an exceptional researcher and learner
- Knowledge of Linux is must to handle PT distros such as Backtrack/Kali
- Certifications show he's willing to invest time to learn concepts and build his concepts and foundations. Security Conferences attendance shows his like-mindedness to mingle with hackers and keep upto date with trending hacker world.
Above points can be taken as a sampling basis.A lot more goes into making oneself a great hacker and researcher!
Read Other Tutorials
Read All Tutorials »
Flutter in Mobile App development - Pros & Cons
Read Details »
3 Signs Your Twitter Account Has Been Hacked & How To Recover It
Read Details »
How to check a suspicious link without clicking on it?
Read Details »
ATM Skimming: The latest high-tech ATM Fraud in Kolkata
Read Details »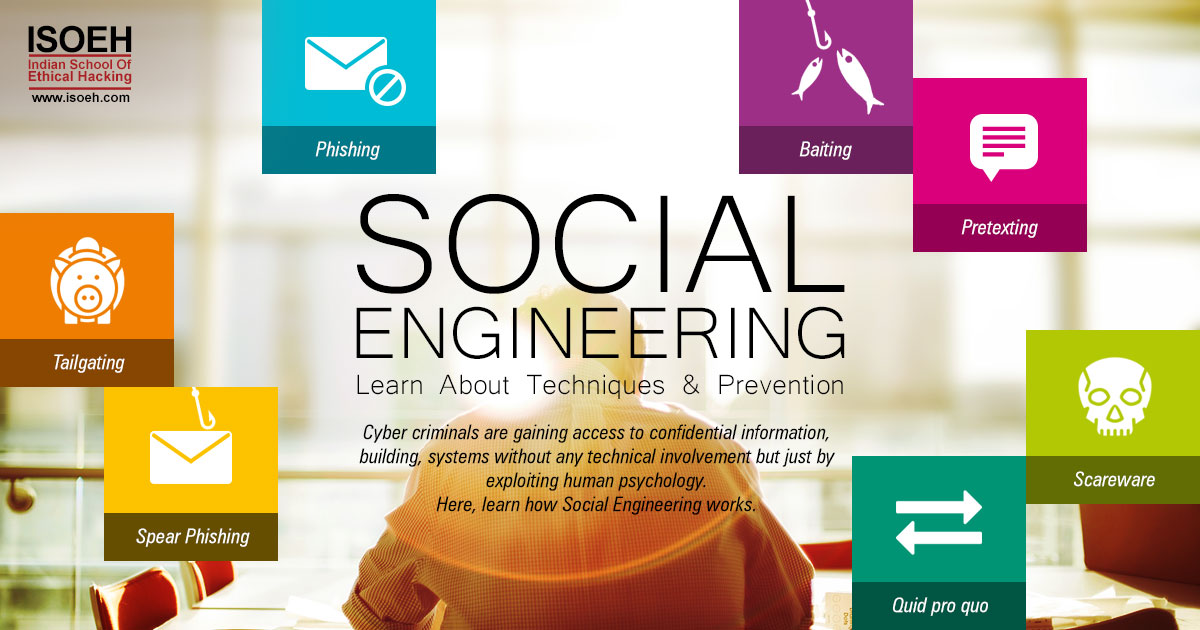
Social Engineering – learn about Techniques & Prevention
Read Details »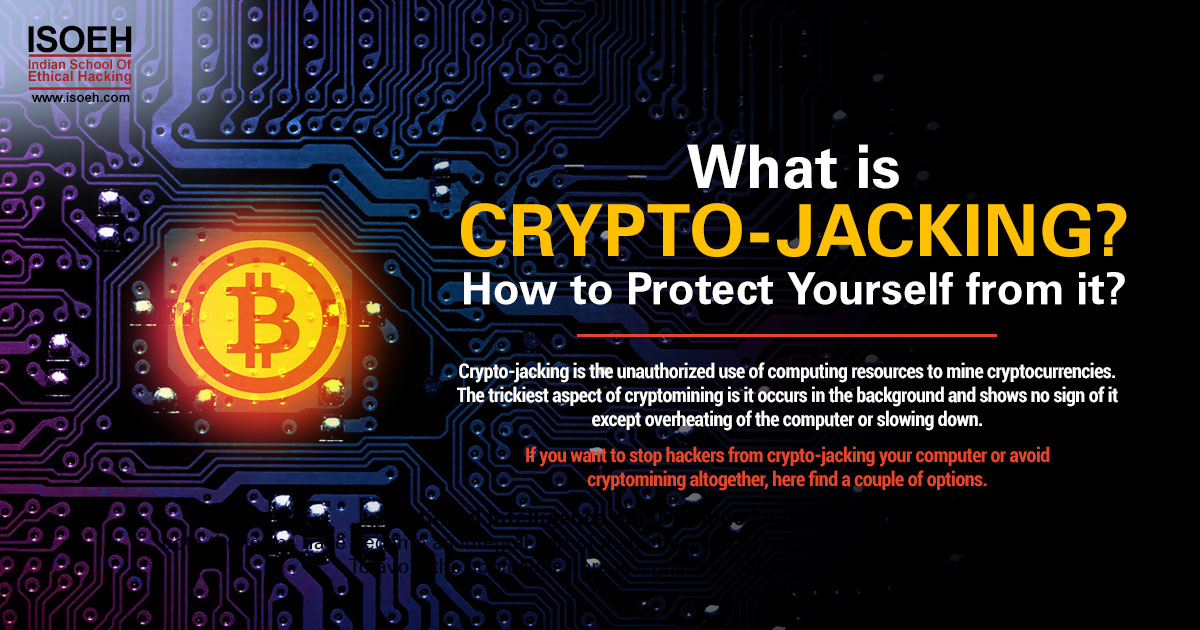
What is crypto-jacking? How to protect yourself from it?
Read Details »
Artificial Intelligence & Machine Learning – What's the difference between them?
Read Details »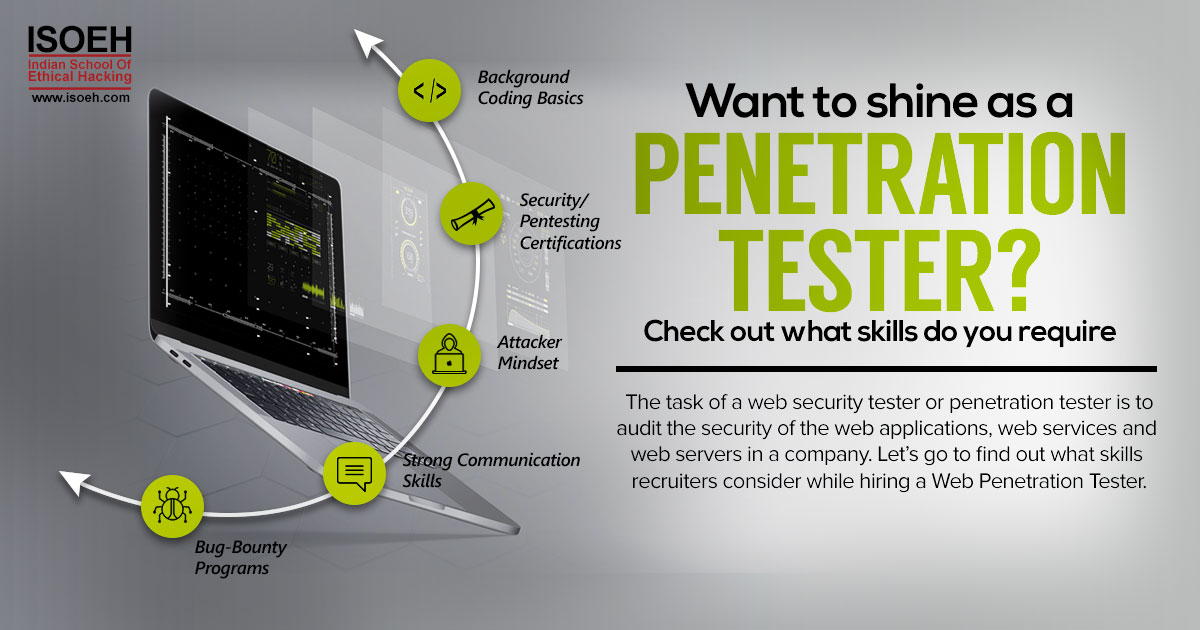
Want to shine as a Penetration Tester? Check out what skills do you require
Read Details »
Machine Learning, the booming career option shaping the job market
Read Details »
Tips to Become an Ethical Hacker with CEH v9 Bootcamp!
Read Details »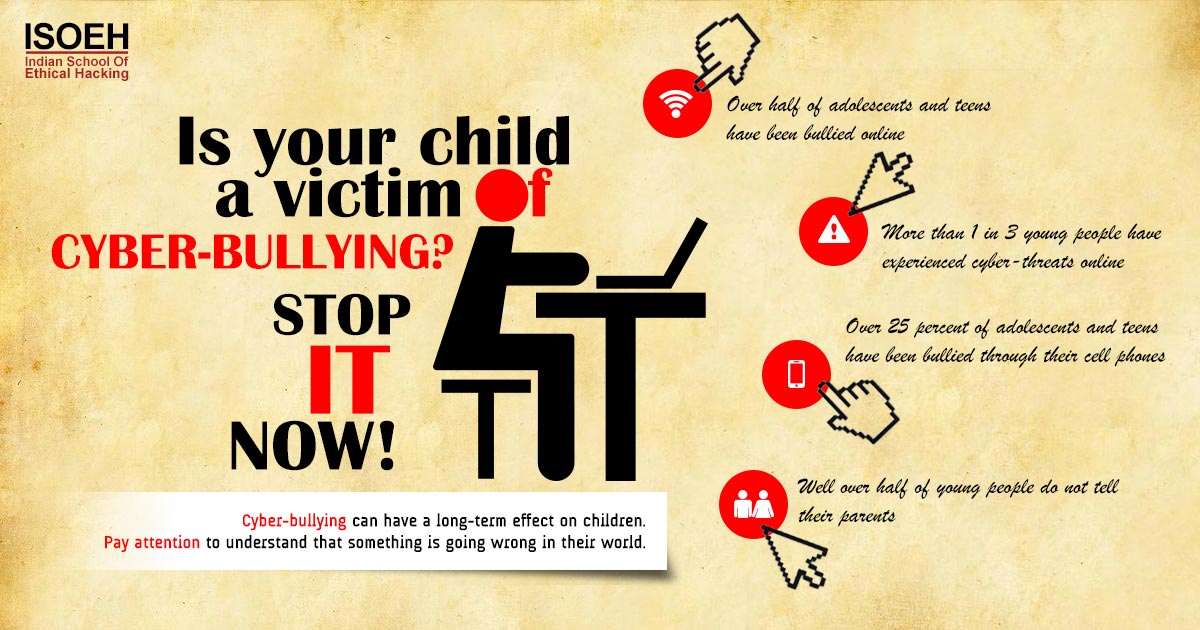
Is your child a victim of cyber-bullying? Stop it now!
Read Details »
5 terrifying ways your phone can get hacked
Read Details »
Want to become a successful bug bounty hunter? Follow the steps!
Read Details »
Top 5 Wifi hacking tools
Read Details »
Quick tip: For all those annoyed with utorrent ads
Read Details »
IDS - Intrusion Detection Systems" title="IDS - Intrusion Detection Systems
Read Details »
Payment Card IndustryData Security Standard in nutshell
Read Details »
What goes into selecting a Web Pentesting consultant?
Read Details »>
<
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read DetailsSubscribe for newsletter
Our Top Courses:
>
<

