For Enquiry, please email us info@isoeh.com
For any complaint, write directly to CEO - sandeep@isoeh.com


Courses
Home
- All Courses
- CompTIA Global Courses
-
EC-Council Global Courses
- Certified Ethical Hacker - CEH v13 - AI Powered
- CEH Master
- Certified Penetration Testing Professional - CPENT
- CHFI v11 - Computer Hacking Forensic Investigator
- Certified SOC Analyst (CSA)
- Certified Cybersecurity Technician - CCT
- Certified Cloud Security Engineer - CCSE
- Web Application Hacking and Security - WAHS
- Certified Network Defender - CND v2
- EC-Council - Cyber Security Programs
- Post Graduation Courses
- Graduation Courses
- PG Diploma Courses
- Diploma Courses
- Vocational Training Courses
-
Skill Development Short Term Courses
- Ethical Hacking
- Computer Forensic
- SOC Analyst Fundamental
- Core Python Programming
- Advanced Python Programming
- CCNA Essentials & Ethical Hacking Combo
- Web Application Penetration Testing Level I
- Web Application Penetration Testing Level II
- Network Penetration Testing Level I
- Network Penetration Testing Level II
- Reverse Engineering & Malware Analysis
- Bug Bounty Hunting
- CCNA Essential
- Firewall Administration
- A-Z Defense in Comp Security - For Corporates
Bhubaneswar: +91 8100442829
Siliguri: +91 9007392360, +91 8100442827
PMapper - A Tool For Quickly Evaluating IAM Permissions In AWS
Require Further Information 22 Aug, 2018
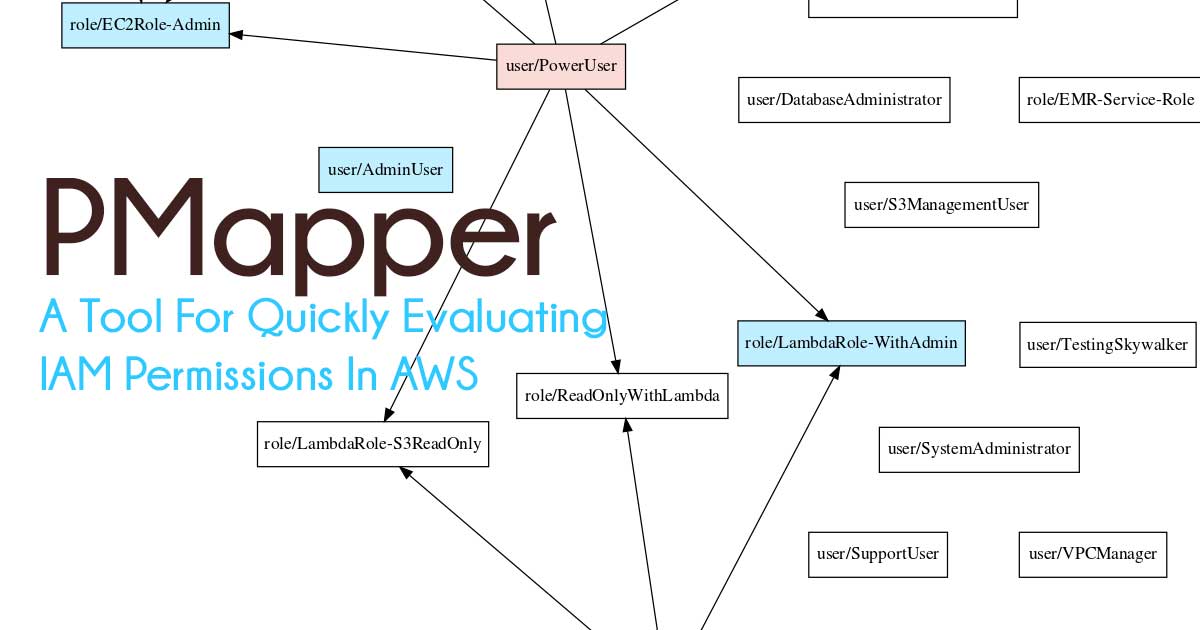
The goal of the AWS IAM auth system is to apply and enforce access controls on actions and resources in AWS. This tool helps identify if the policies in place will accomplish the intents of the account's owners.
How to Use:
- Download this repository and install its dependencies with pip install
-r requirements.txt. - Ensure you have graphviz installed on your host.
- Setup an IAM user in your AWS account with a policy that grants the necessary permission to run this tool (see the file mapper-policy.json for an example). The ReadOnlyAccess managed policy works for this purpose. Grab the access keys created for this user.
- In the AWS CLI, set up a profile for that IAM user with the command:
aws configure --profile < profile_name >where < profile_name > is a unique name. - Run the command
python pmapper.py --profile < profile_name >graph to begin pulling data about your account down to your computer.
Download here: https://github.com/nccgroup/PMapper
Other Hacking Tools
Explore All Hacking Tools »
Pftriage - Python Tool And Library To Help Analyze Files During Malware Triage And Analysis
Read Details »
ADAPT - Tool That Performs Automated Penetration Testing For WebApps
Read Details »
Stardox - Github Stargazers Information Gathering Tool
Read Details »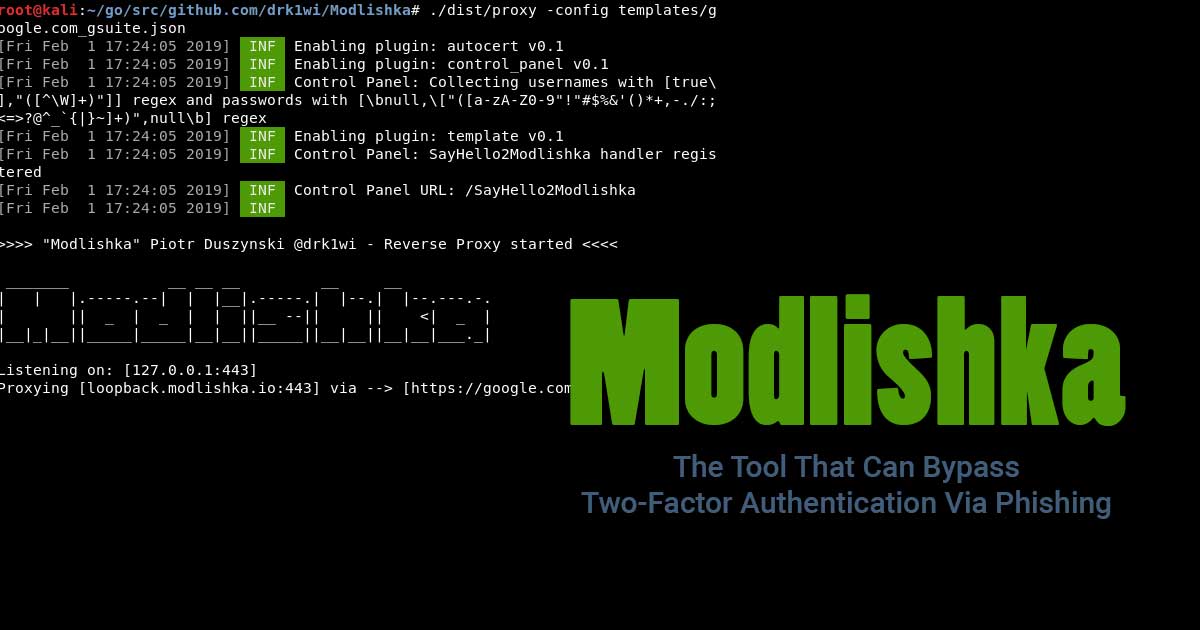
Modlishka - The Tool That Can Bypass Two-Factor Authentication Via Phishing
Read Details »
Stretcher - Tool Designed To Help Identify Open Elasticsearch Servers That Are Exposing Sensitive Information
Read Details »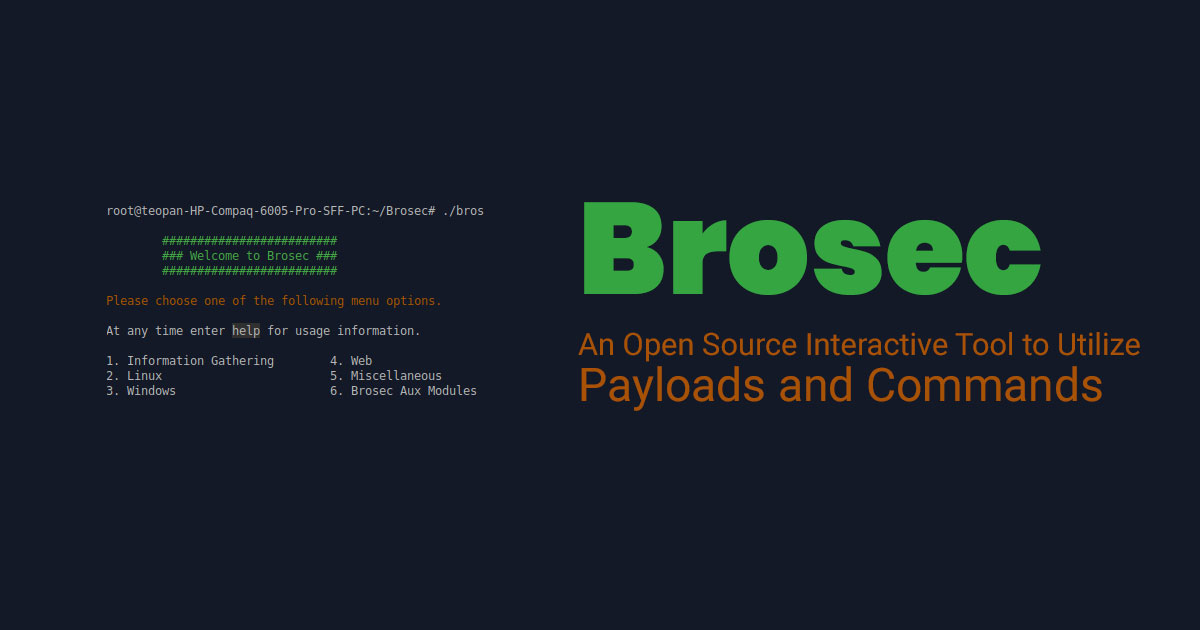
Brosec – An Open Source Interactive Tool to Utilize Payloads and Commands
Read Details »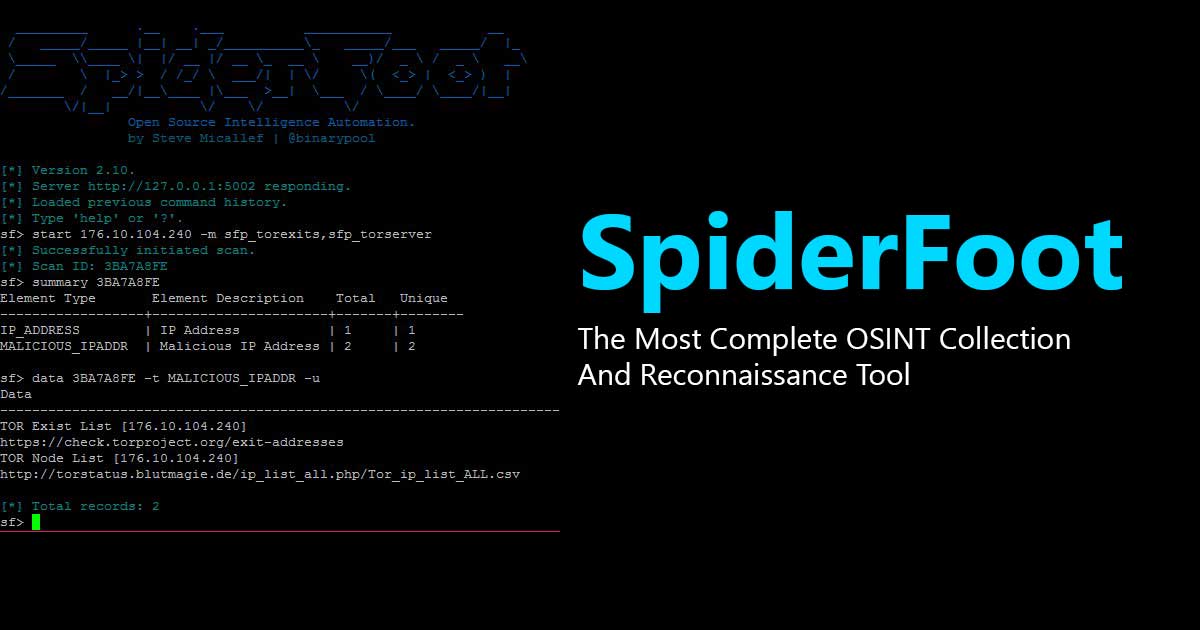
SpiderFoot - The Most Complete OSINT Collection And Reconnaissance Tool
Read Details »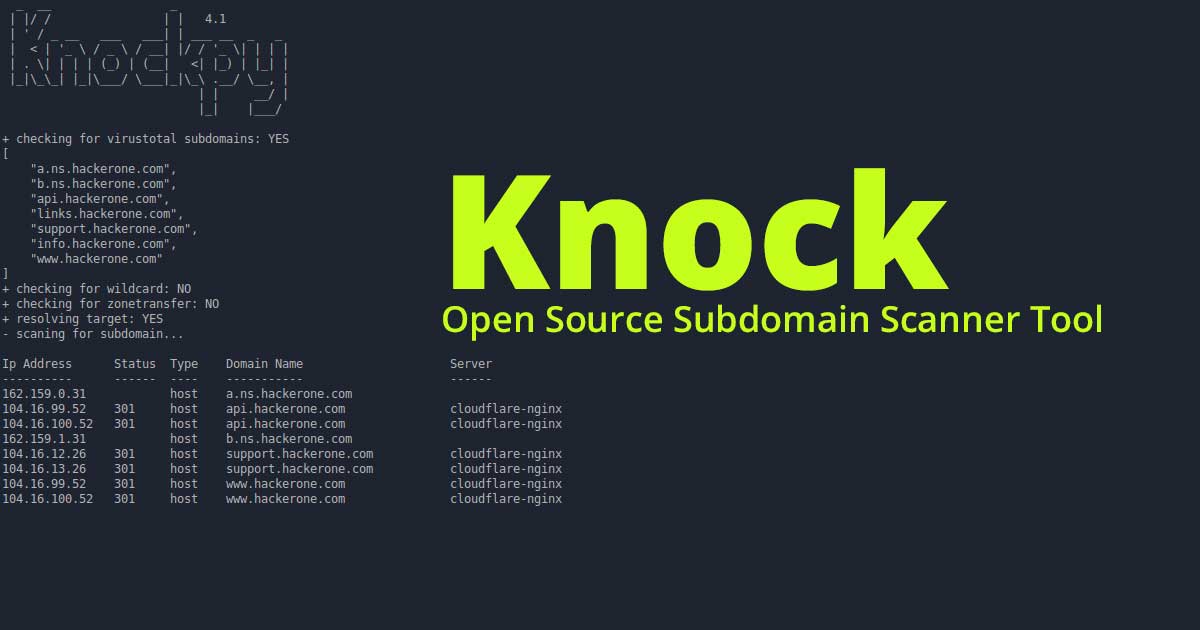
Knock - Open Source Subdomain Scanner Tool
Read Details »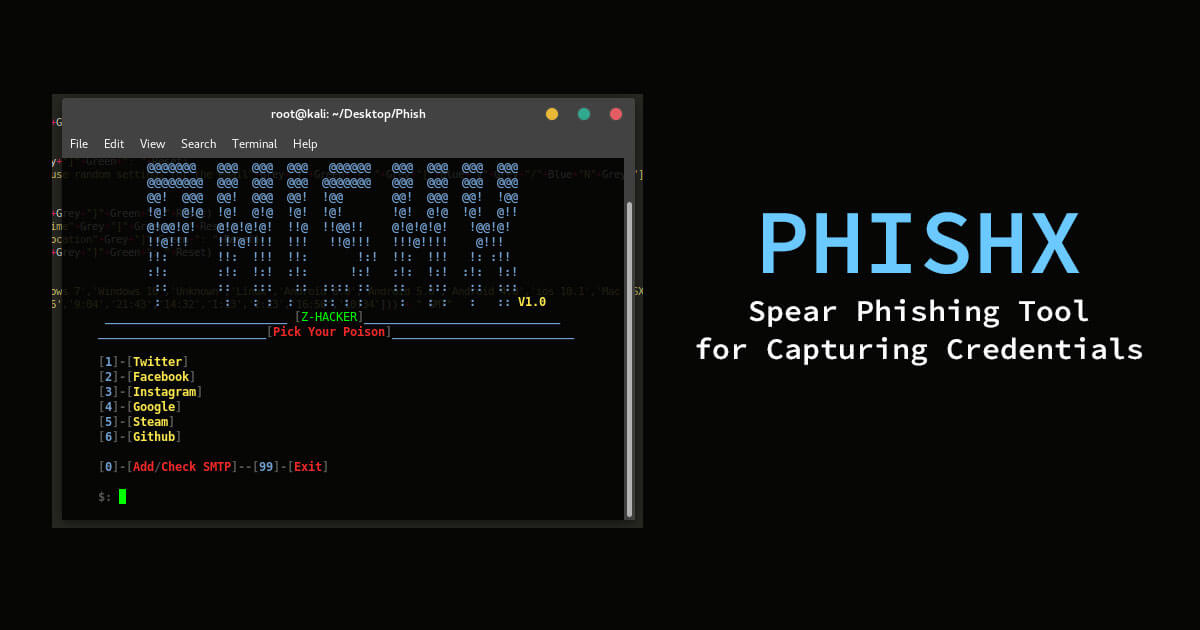
PhishX - Spear Phishing Tool for Capturing Credentials
Read Details »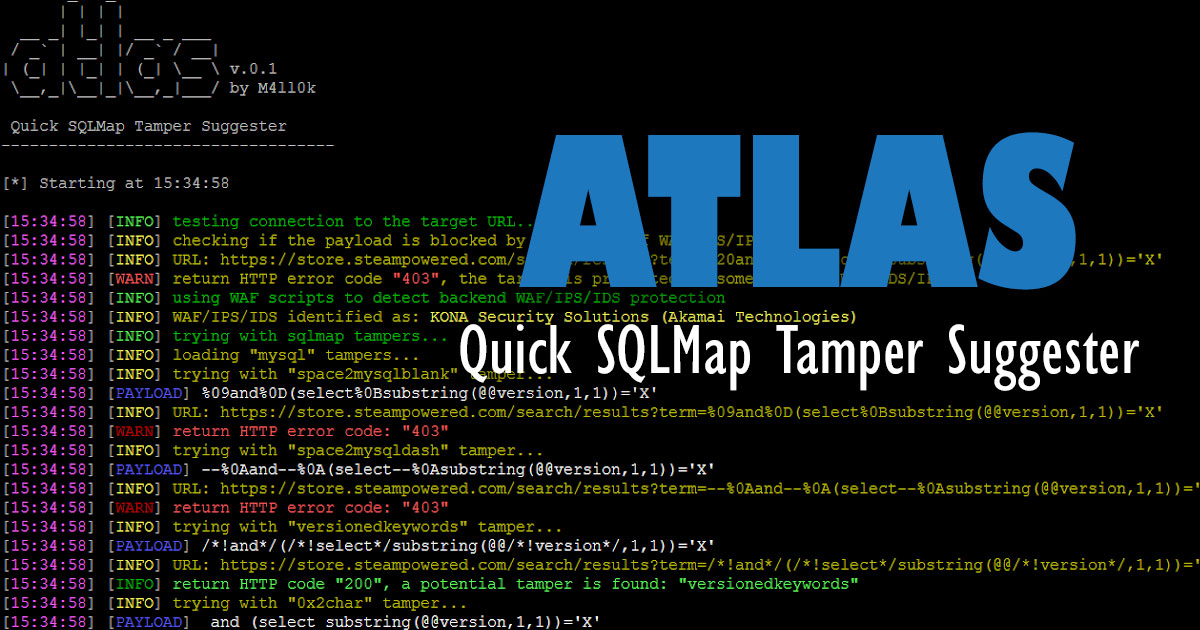
Atlas - Quick SQLMap Tamper Suggester
Read Details »
XenoScan - Open Source Memory Scanner Written In C++
Read Details »
Ettercap - A Comprehensive Suite For Man In The Middle Attacks
Read Details »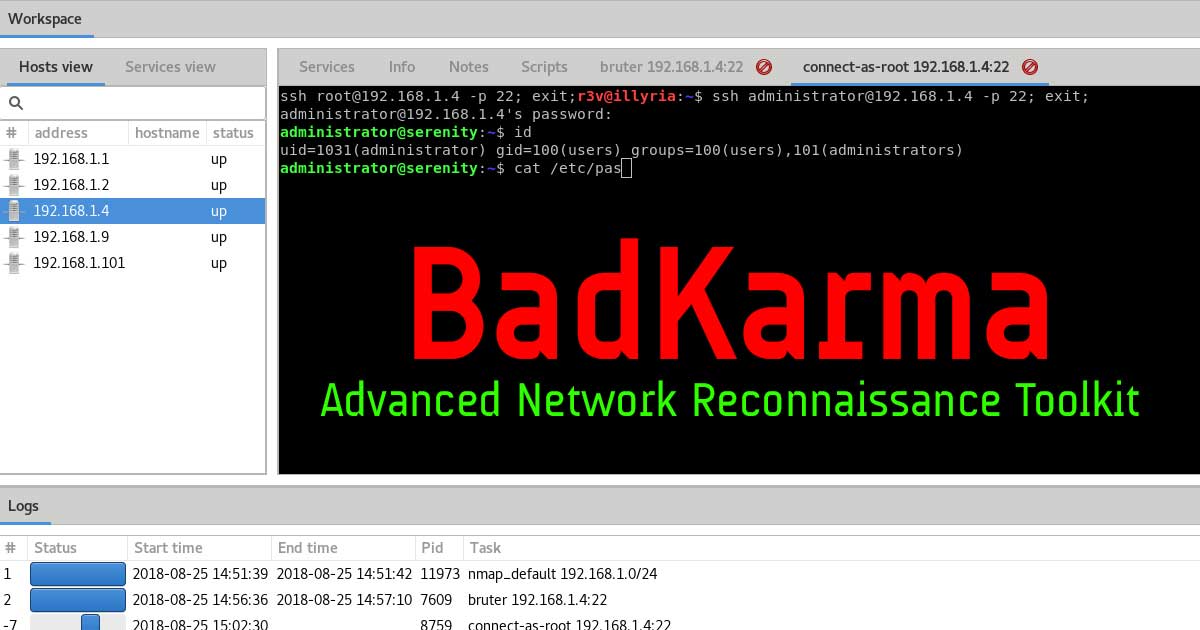
BadKarma - Advanced Network Reconnaissance Toolkit
Read Details »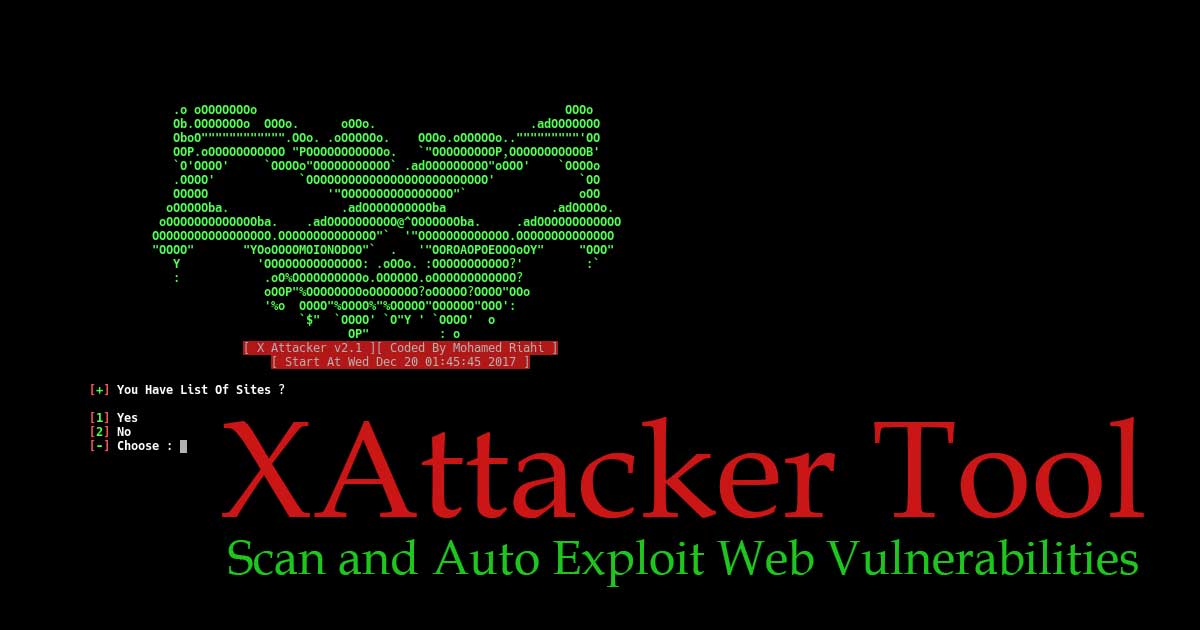
XAttacker Tool – Scan and Auto Exploit Web Vulnerabilities
Read Details »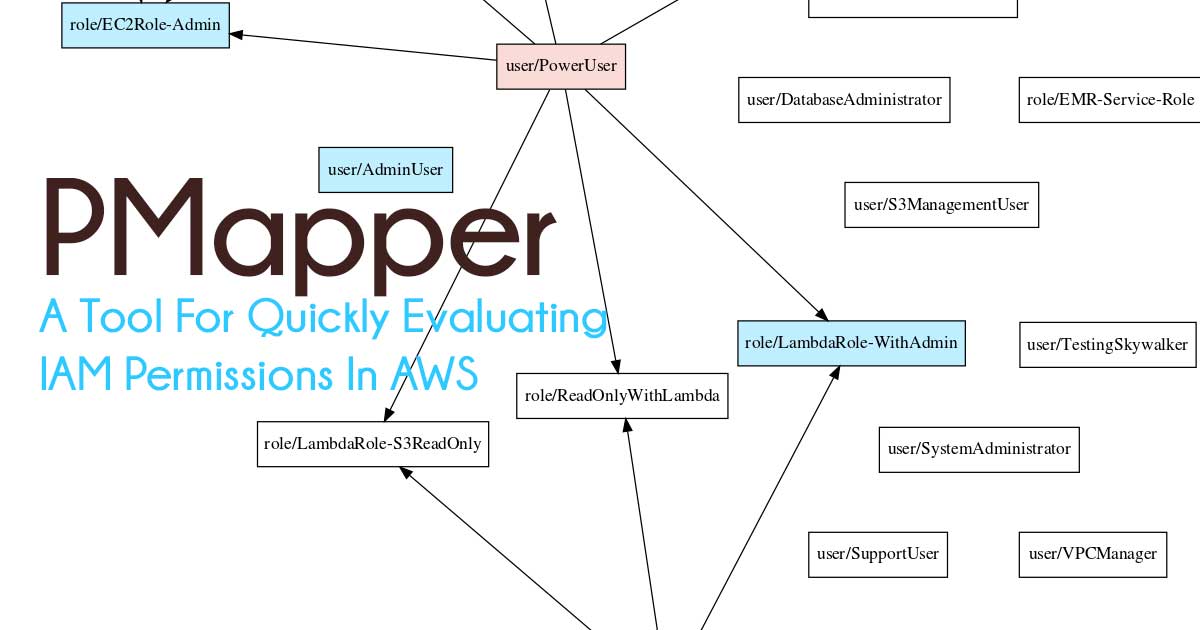
PMapper - A Tool For Quickly Evaluating IAM Permissions In AWS
Read Details »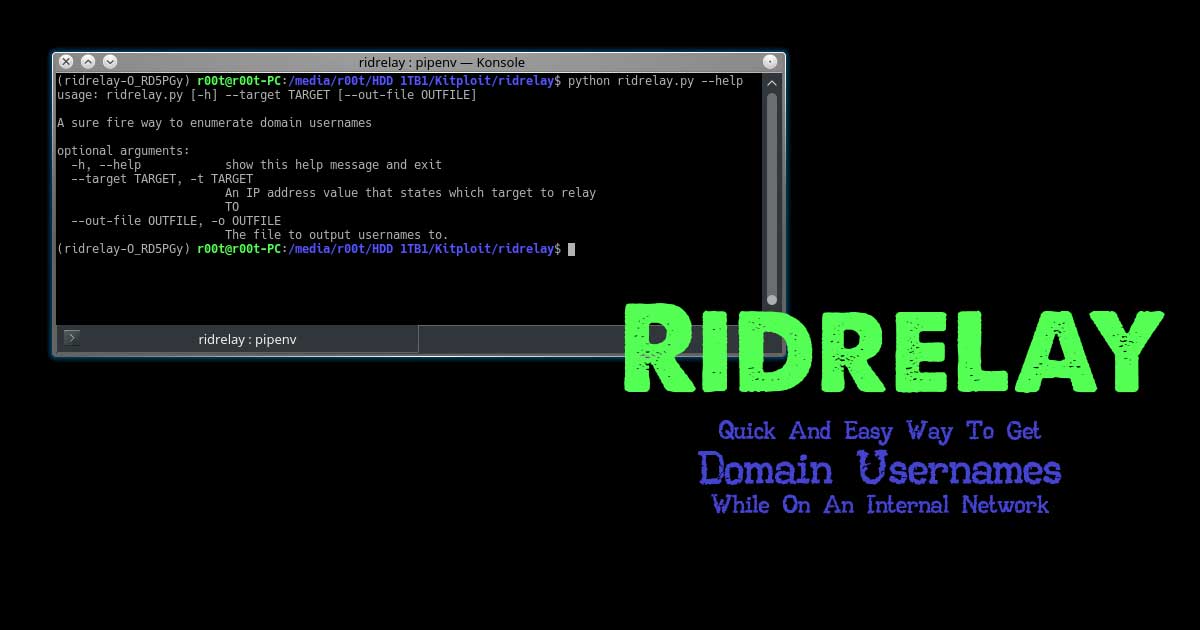
Ridrelay - Quick And Easy Way To Get Domain Usernames While On An Internal Network
Read Details »
PhpSploit - Stealth Post-Exploitation Framework
Read Details »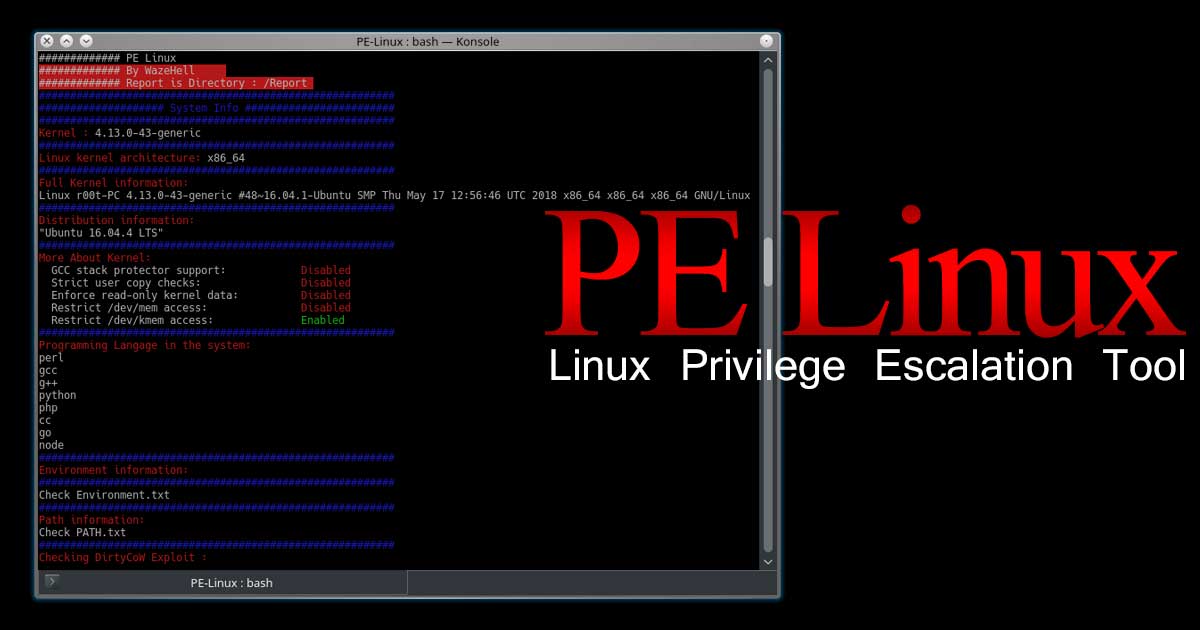
PE Linux - Linux Privilege Escalation Tool
Read Details »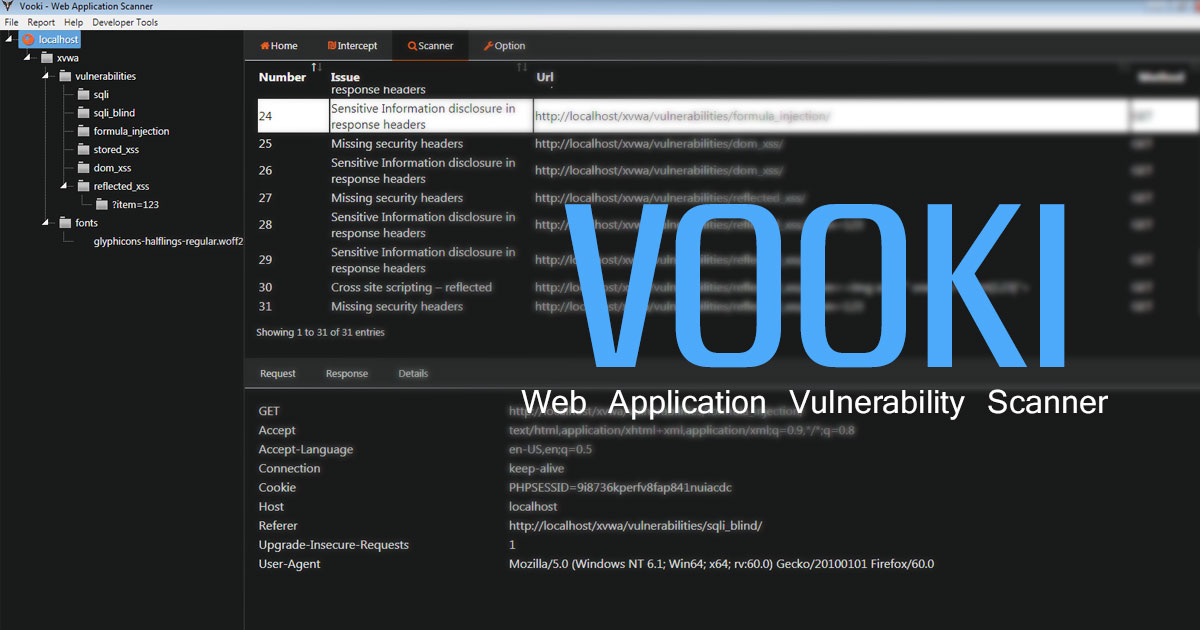
VOOKI - Web Application Vulnerability Scanner
Read Details »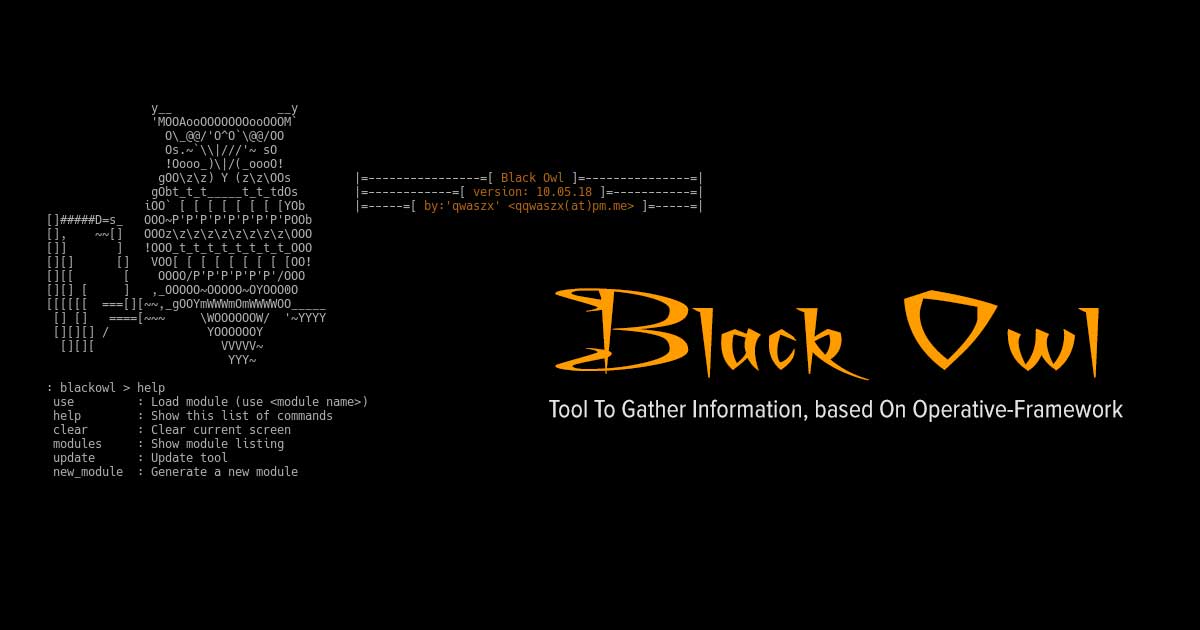
Black Owl - Tool To Gather Information, based On Operative-Framework
Read Details »
MSDAT - Microsoft SQL Database Attacking Tool
Read Details »
Autopwn v2.0 : Metasploit Automation Tool
Read Details »
GPON - Python Exploit For Remote Code Executuion On GPON Home Routers (CVE-2018-10562)
Read Details »
Mimic - A Tool For Covert Execution In Linux
Read Details »
Aircrack - the password cracking tool
Read Details »
CLOUDKiLL3R - Bypasses Cloudflare Protection Service Via TOR Browser
Read Details »
VoIP Sniffer: UCSniff
Read Details »
OWASP ZSC – Obfuscated Code Generator Tool
Read Details »
Sublist3r – Fast Python Subdomain Enumeration Tool
Read Details »
Acunetix WVS
Read Details »
Wireshark: Web vulnerability scanner
Read Details »
UFTP - UDP based FTP with encryption
Read Details »
Android hacking 'APK'
Read Details »
Executable Compression demystified
Read Details »
BitCracker – Password Cracking Tool
Read Details »
BloodHound – Red / Blue teaming tool for AD attacks
Read Details »>
<
Exclusive Blog
Read All Exclusive Blog »
With world working from home, it's time to make it enjoyable and effective.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details
