
Application security in the cloud is a series of defined policies, processes, controls, and technology guiding all information exchanges that happen in collaborative cloud environments like Microsoft Office 365, Google G Suite, 'Slack and Box' etc. So, if any company employee frequently stores and shares data in cloud applications like the ones listed above (or any other such cloud storage available), it is absolutely necessary to add a cloud application "safety net" to themistrust security infrastructure.
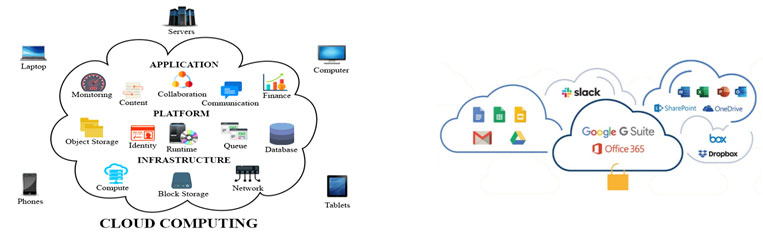
The industry market analysts always like to create newer versions of security markets, where the goal should be to combine findings across the various components of the application and cloud infrastructure into a single, DevOps user-friendly tool to prioritize and amend vulnerabilities quickly. Some tools emerge in two areas: Application Security and Cloud Security.
In the case of Application Security, the following are being consolidated: *- Custom Code (i.e., static and dynamic analysis)
- Open Source/Third Party Code (i.e., software composition analysis)
- Orchestration/Containers (i.e., endpoint security, Kubernetes security, and container security)
- Cloud Infrastructure (i.e., infrastructure as code, cloud workload protection, and cloud security posture management)
- Orchestration/Containers (i.e., container security and serverless)
- Application Programming Interfaces (i.e., web application firewalls and API security)
- Visibility, Compliance, and Governance
- Threat Detection
- Data Security
- Host Security
- Container Security
- Serverless Security
- Web Application and API
- Identity-Based Micro-segmentation
- Identity and Access Management Security
Most Common Cloud App Security Threats:
It is obvious that there are security issues in cloud computing that IT teams must be aware of. According to the 2018 Cybersecurity Insider Report, the four most common cloud application security threats that IT teams are facing are:
- Misconfiguration of application setup is the single biggest threat to cloud computing security because data breaches tend to happen when services are accidentally exposed to the public internet.
- Unauthorized access to a website, server, service, or other system is also an area of great concern because once they're in, there's no telling what unauthorized users will do to create chaos.
- Insecure APIs and interfaces present easy opportunities for attackers to breach systems because they are the only asset(s) outside of the organizational boundary with a public IP address.
- Account hijacking is feared because so much sensitive data and resources are stored and accessed on devices shared by many different users—and because keeping tabs on rogue employees is difficult.
Cloud Application Security Options:
A common misconception in today's digital world is that it requires a proxy, browser extension, or some other agent to secure cloud applications. However, there are cloud security solutions available that allow a cloud application's native APIs to monitor, control, and secure activity within them. The two basic options on the market available are between an API vs proxy CASB. API-based cloud application security platforms (CASP) are quickly becoming the favored security model for every admin.This occurs for three main reasons:
- A CASP doesn't need to route access through a third party or proxy server, so it doesn't impact end users' experiences in the speed of access or network performance.
- Like a proxy-based solution, CASP provides an add-on layer of security to theframework. They perform well with existing network security appliances, like the firewall, by providing an extra level of security and control over the information stored in cloud applications, which a firewall or gateway can't provide alone. A proxy-based cloud access security broker (CASB) solely duplicates the functionality of a firewall and inserts it between the users and the applications to do jobs.
- Particularly, Google and Microsoft have both published suggestions against their use. The primary reason is due to a CASB's inability to stay informed as they make upgrades to their application infrastructures; application developers make changes to protocols, authentication methods, and on a regular basis.
It's worth noting that few cloud security providers use Chrome browser extensions, rather than athird-party cloud, to secure cloud access. It is termed as "agentless" cloud security, but the extension is a different type of proxy. Traffic will still run through it, and they will face the same drawbacks as other CASBs. Moreover, Google is planning a major rebuild of Chrome extension support that could lead the whole technology through a loop.
Cloud application security platforms, work as a nearly local feature within each cloud application. They create intense one-to-one integrations using the cloud applications APIs (sometimes in close partnership with the application provider). Only changes in API protocols can affect the efficacy of a CASP, and those changes are constantly documented and updated for developers.
API's role in cloud security:
CTOsand CISOs can leverage API-based cloud application security platforms to roll with the punches without skipping a beat. These advanced platforms can also easily detect existing and/or new risks in cloud applications which is based on changes in OAuth permissions settings, customer complaints, security reports, and many more.
The SaaS vendor and the customer (we) are in charge of Cloud Application Security. Cloud security is a top risk factor that IT managers quote as themain barrier to cloud transformation. But, for the vast majority of organizations and industries, the benefits to a degreeexceed the risks. There are many ways to build an effective cloud computing security infrastructure, and securing the data created, stored, and accessed in company cloud applications is a greater part of that.The timeframe when an organization transitions to the cloud, it outsourced some of the more hybrid architecture and server security operations to another vendor (sometimes, to a vendor with large-scale and better-funded security teams, for example, Google and Microsoft).
*Source:(https://securityweekly.com/)
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details
















