
Phishing is no longer about spelling mistakes and shady email links. The new wave of attackers is exploiting something far more dangerous — Microsoft's own trusted infrastructure. Welcome to Active Directory Federation Services hijacking, a phishing campaign so deceptive that even seasoned professionals struggle to spot it.
Let's learn about Active Directory Federation Services Hijacking!
Active Directory Federation Services (ADFS) hijacking is a novel phishing technique where hackers abuse Active Directory Federation Services and the office.com domain itself to redirect unsuspecting users into perfectly cloned phishing sites.
Unlike traditional phishing, where suspicious URLs raise red flags, this method makes the attack chain begin with legitimate Microsoft domains, giving it a cloak of absolute trust.
So, In short: Hackers weaponize Microsoft against Microsoft.
Do you know the anatomy of the office.com Phishing Attack Chain?
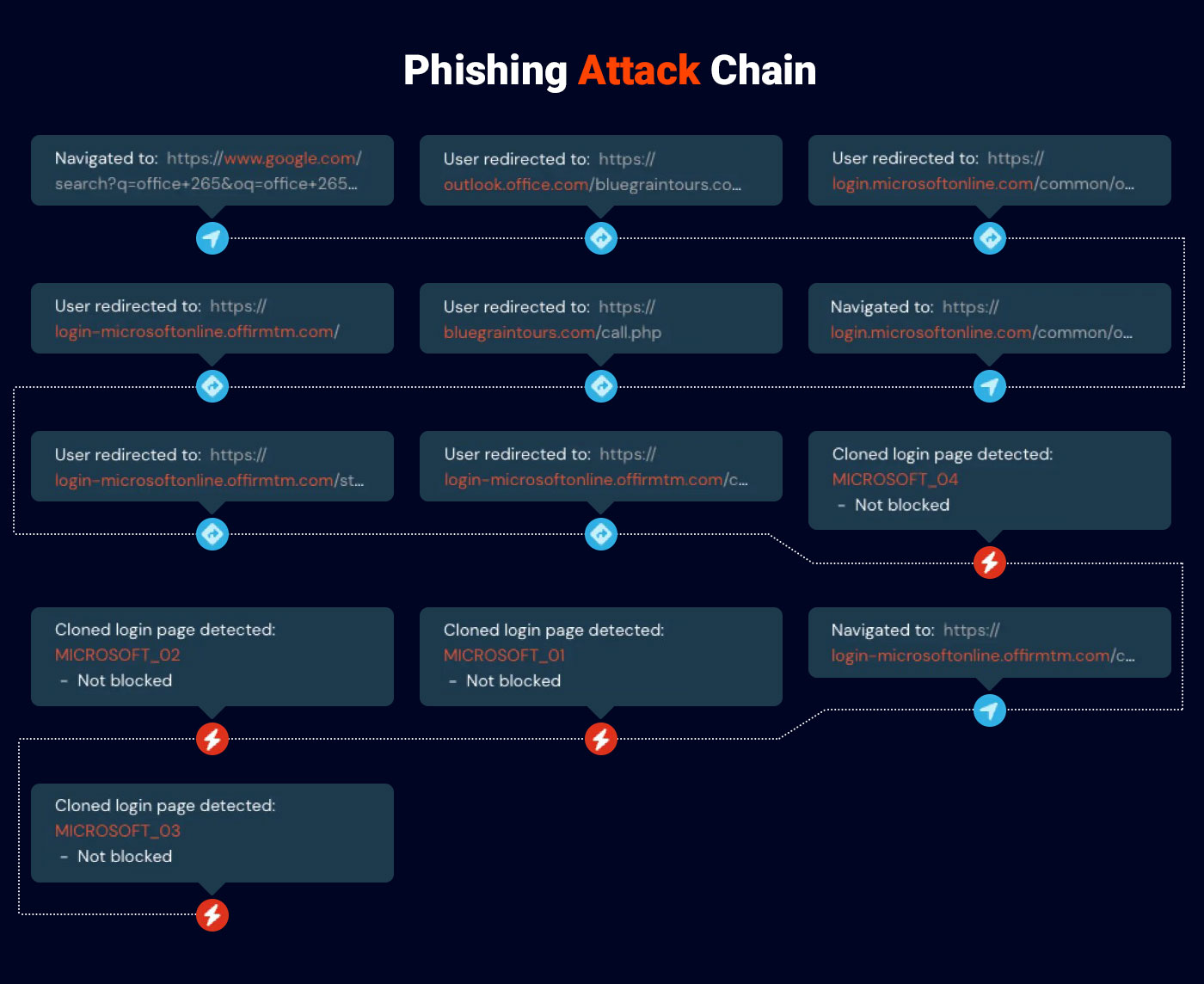
Let's break down the full attack path step by step for you— the process based on which cyber experts or SOC investigator would analyse it:
1. Malvertising as the Initial Lure
- Victims search Google or Bing for "Office 365 login."
- They click on a sponsored ad that looks completely genuine.
- The ad points to a real outlook.office.com URL — nothing suspicious yet.
2. Active Directory Federation Services Abuse Begins
- Hackers are now ready to set up their own Microsoft tenant.
- They configure Active Directory Federation Services redirect rules to forward login requests to their own malicious site.
- Microsoft servers now hand victims over the cybercriminals unknowingly.
3. The Hidden Redirect Chain
- Before hitting the fake login, the browser silently hops through intermediary domains (like fake blogs or harmless-looking websites).
- This deceives automated URL reputation engines into thinking the link is safe.
4. The Pixel-Perfect Fake Login Page
- Victims land on what looks like an authentic Microsoft 365 login page.
- Entering credentials here sends usernames, passwords, and session cookies straight into attacker-controlled servers.
5. MFA Defeated with Session Hijacking
- With session cookies, hackers bypass multi-factor authentication (MFA).
- They gain full access to mailboxes, files, Teams, and everything in Microsoft 365.
So, this is not just phishing — it's a full Attacker-in-the-Middle (AitM) campaign wrapped in Microsoft's own trust.
Why office.com and Active Directory Federation Services Hijacking Works So Well
- Trusted Domains: The attack begins at office.com, domain users inherently trust.
- No Email Delivery: By skipping phishing emails, it bypasses secure email gateways entirely.
- Malvertising Advantage: Ads give attackers a new, scalable distribution channel.
- MFA Bypass: Stolen cookies render even strong authentication useless.
Defense Playbook Against Active Directory Federation Services Exploitation
If you're defending against this campaign, here's your practical response strategy:
Monitor Active Directory Federation Services Logs
- Check for unfamiliar redirect URIs in authentication events.
- Investigate anomalies where office.com redirects out to non-Microsoft domains.
Block Malvertising Entry Points
- Deploy enterprise-wide ad blockers on browsers.
- Train users to type login URLs manually instead of relying on ads.
Analyze Traffic for Red Flags
- Filter Google Ad referral parameters going into office.com.
- Hunt for traffic bouncing off unrelated sites (blogs, hobby pages, travel portals).
Harden Authentication
- Adopt phishing-resistant MFA (FIDO2 keys, hardware tokens).
- Use Conditional Access policies to detect suspicious cookie replays.
Key Lessons for Students & Professionals
This case study of Active Directory Federation Services hijacking is a must-know attack chain for anyone entering or working in cybersecurity:
- Students: Learn how attackers don't always exploit code — they exploit trust and design gaps.
- Professionals: Traditional filters won't save you; detection must go deeper into behavioral and redirect analysis.
- Red-Teamers: This is an example of how abusing native infrastructure can outperform "classic" phishing methods.
Just one reminder: attackers don't always need a zero-day. Sometimes, they just need a clever abuse of what's already trusted.
One last final word:
Active Directory Federation Services hijacking proves that the biggest risk isn't always a vulnerability — it's misplaced trust. By manipulating Microsoft's own Active Directory Federation Services and office.com infrastructure, hackers have created a phishing attack almost impossible to detect by eye.
Cybersecurity experts remind defenders of a hard truth: protection can't stop at domains and emails. Detecting suspicious redirects, enforcing phishing-resistant MFA, and adopting proactive ad-blocking are no longer best practices — they're survival essentials.
Keep your guard up. Trust, but always verify — because even office.com can betray you.
Hacking Tools
Explore All Hacking Tools »
UFTP is an encrypted multicast file transfer program for secure, reliable & efficient transfer of files. It also helps in data distribution over a satellite link.
Read DetailsBreaking News
Breaking News Of Each Month »
The recent pandemic was unexpected and unknown to most part of the world. It has changed our life and we are slowly adapting to our new lifestyle. The risks associated with the new lifestyle, both personal & corporate, are unknown to most of us.
Read Details
















