YouTube Live on Advanced Ethical Hacking & Cyber Security on 16th Sept 2021 @ 3PM
By ISOEH
Published on: 16 Sep, 2021
View On YoutubeEmerging Technologies & Emerging Jobs - AICTE SPONSORED ATAL ADVANCED FDP ON "IOT & CYBER SECURITY"
By ISOEH
Published on: 15 Sep, 2021
View On Youtubeব্যাঙ্ক প্রতারণার অভিযোগে পুলিশের জালে ধরা পড়ল জামতাড়া গ্যাং-এর বড় দল। - ISOEH Live on ABP Ananda
By ISOEH
Published on: 09 Sep, 2021
View On YoutubeCyber Fraud - ফেসবুক চ্যাট এ ব্ল্যাকমেল এর ফাঁদ! Mr. Sandeep Sengupta Live on ABP Ananda Exclusive
By ISOEH
Published on: 06 Sep, 2021
View On YoutubeHow to Configure Extended Access List in Packet Tracer
By Mr. Saumitra Biswas - ISOEH Faculty
Published on: 27 Aug, 2021
View On YoutubeISOEH Cyber Expert Mr. Samyajit Mukherjee Discussing the Career Opportunity of the Bsc Cyber Security course on Facebook Live Program.
By Netaji Subhash Engineering College
Published on: 22 Aug, 2021
View On FacebookHow We Can Track a Macro Based Malware?
By Mr. Debraj Basak - Information Security Research Analyst
Published on: 21 Jul, 2021
View On YoutubeISOAH Data Securities Pvt. Ltd. Director Mr. Sandeep Sengupta discussing on Cyber Threats in Post Pandemic World at MSME & Startups Forum – Bharat
By MSME & STARTUPS FORUM - BHARAT
Published on: 18 Jul, 2021
View On YoutubeISOAH Cyber Expert Mr. Samyajit Mukherjee Live on News Time Bangla, Discussing The SBI Banking Fraud
By ISOEH
Published on: 16 Jul, 2021
View On YoutubeISOAH Cyber Expert Mr. Samyajit Mukherjee Live on News18 Bangla, Discussing The SBI Banking Fraud
By ISOEH
Published on: 16 Jul, 2021
View On YoutubeTutorials
Read All Tutorials »
Building a career in Digital Forensics - How promising is the future? A thorough career guide
Read Details »
Why participating in Hackathons is a good idea?
Read Details »Hacking Tools
Explore All Tools »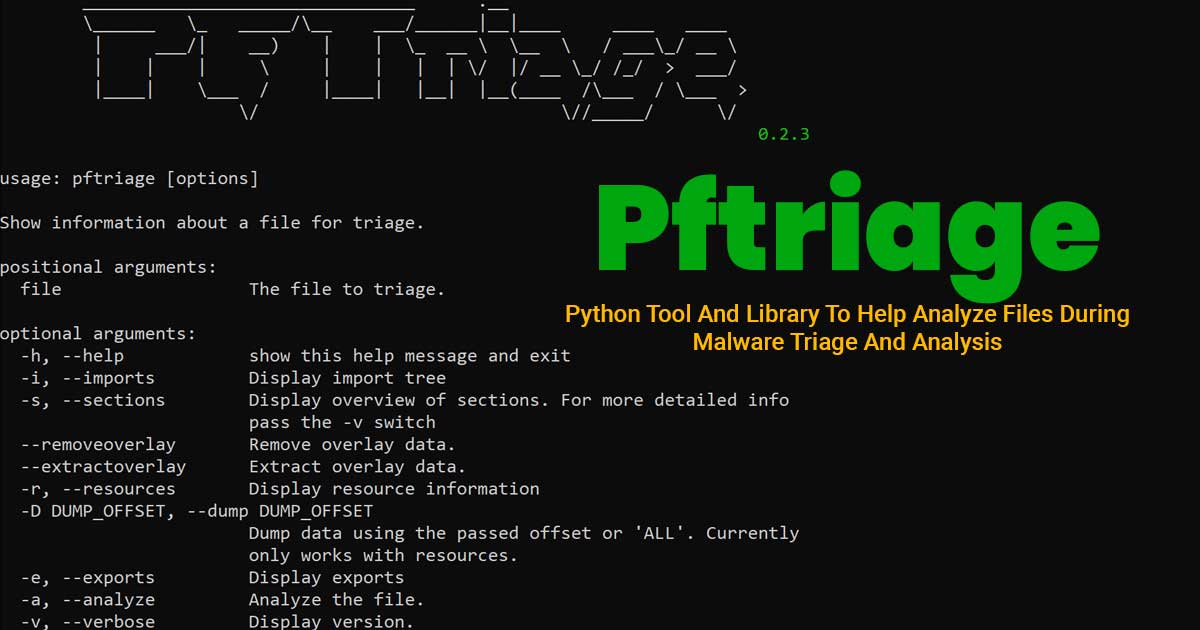
Pftriage - Python Tool And Library To Help Analyze Files During Malware Triage And Analysis
Read Details »