Next Offline Hackathon Schedule
Don't miss this!
Date:
Coming soon
Coming soon
Venue:
ISOEH Kolkata Campus
Kariwala Towers, 4th Floor, Plot J/1-5, Block EP, Sector V, Salt Lake City, Kolkata - 700091
ISOEH Kolkata Campus
Kariwala Towers, 4th Floor, Plot J/1-5, Block EP, Sector V, Salt Lake City, Kolkata - 700091
Who can Participate?
From amateur Hackers to Professional Techies
Certificate of Participation
Will be given to all participants
An initiative by
to spread Cyber Security Awareness in India.
We are
Accredited Training Center by


Authorized Test Center of
ISO 9001:2015 Certified by


ISO 27001:2022 Certified by


CERT-In Empanelled Security Auditor


Member of


Hackathon Rules
- Time based CTF challenge.
- Consisting of hacking into VMs, CTF, IoT, Reverse Engineering.
- Open freestyle method.
- All tools allowed.
- Offline Hackathon.
- No Team. Single Participant is ALLOWED.
- No AGE restrictions.
At the same time, parallel to completing the hacking steps, you will be given a vulnerable VM (always connected to LAN), which you have to defend. Negative marks if you get hacked by other competitors.
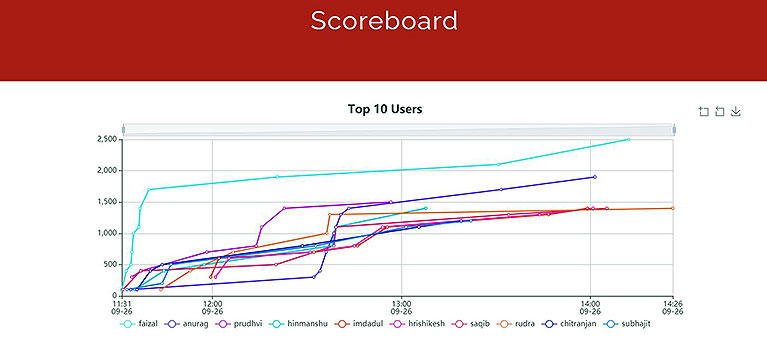
Hackathon Ongoing

Previous Hackathon
North Bengal Hackathon Event at ISOEH Siliguri Centre – Local TV News Coverage by News10Bangla
North Bengal Hackathon Event at ISOEH Siliguri Centre – Local TV News Coverage by CCN TV